从文章一将各个算法整合:
文章(一)算法传送门:
https://blog.csdn.net/weixin_38927522/article/details/123799022
如下整合的c++代码 run.cpp:.
源码传输门地址:
https://wwi.lanzoup.com/izAEa027198d
#define __USE_GNU
#include <iostream>
#include <cstdlib>
#define __USE_GNU
#include <string>
#include "stdio.h"
#define __USE_GNU
#include "string.h"
#include "stdlib.h"
using namespace std;
//extern char *strdup(char *s);
char *strdup(const char *s)
{
char *t = NULL;
if (s && (t = (char*)malloc(strlen(s) + 1)))
strcpy(t, s);
return t;
}
//#include "xyAes.cpp"
#ifndef XHSSHIELD_XYAES_H
#define XHSSHIELD_XYAES_H
class xyAes {
public:
void testAesDec(char *in,char *out,char *aesKey);
};
#endif //XHSSHIELD_XYAES_H
//#include "xyMd5.cpp"
#ifndef XHSSHIELD_XYMD5_H
#define XHSSHIELD_XYMD5_H
class xyMd5 {
public:
void GenrateResult(unsigned char* url,char* out);
};
#endif //XHSSHIELD_XYMD5_H
//#include "xyXor.cpp"
#ifndef XHSSHIELD_XYXOR_H
#define XHSSHIELD_XYXOR_H
class xyXor {
public:
void GenrateResult(unsigned char* in, unsigned char *out);
};
#endif //XHSSHIELD_XYXOR_H
//#include "base64.cpp"
#ifndef XHS_BASE64_H
#define XHS_BASE64_H
#define BASE64_ENCODE_OUT_SIZE(s) ((unsigned int)((((s) + 2) / 3) * 4 + 1))
#define BASE64_DECODE_OUT_SIZE(s) ((unsigned int)(((s) / 4) * 3))
/*
* out is null-terminated encode string.
* return values is out length, exclusive terminating `\0'
*/
unsigned int
base64_encode(const unsigned char *in, unsigned int inlen, char *out);
/*
* return values is out length
*/
unsigned int
base64_decode(const char *in, unsigned int inlen, unsigned char *out);
#endif //XHS_BASE64_H
// 写法固定,
extern "C" {
// 释放内存
void freeme(char *ptr) {
free(ptr);
}
//char *strdup(const char *s)
//{
// char *t = NULL;
// if (s && (t = (char*)malloc(strlen(s) + 1)))
// strcpy(t, s);
// return t;
//}
// 获取加密参数,有三个参数,返回值是个字符串
char* getXhsShield(char *sXml, char *url, char *aesKey) {
xyAes* xy = new xyAes;
string strMain = sXml;
unsigned char *decode = new unsigned char [strMain.length() / 4 * 3];
(void)base64_decode(strMain.c_str(),strMain.length(),decode);
unsigned char out[256] = {0};
xy->testAesDec(reinterpret_cast<char *>(decode), reinterpret_cast<char *>(out),reinterpret_cast<char *>(aesKey));
delete []decode;
xyMd5* md5 = new xyMd5;
char md5Result[16] = {0};
md5->GenrateResult(reinterpret_cast<unsigned char *>(url),md5Result);
xyXor* xyshield = new xyXor;
unsigned char in[128] = {
0x00, 0x00, 0x00, 0x01, 0xEC, 0xFA, 0xAF, 0x01, 0x00, 0x00, 0x00, 0x02, 0x00, 0x00, 0x00, 0x07,
0x00, 0x00, 0x00, 0x24, 0x00, 0x00, 0x00, 0x10, 0x36, 0x38, 0x37, 0x30, 0x32, 0x31, 0x33, 0x37,
0x30, 0x63, 0x35, 0x39, 0x32, 0x35, 0x39, 0x2D, 0x37, 0x65, 0x39, 0x31, 0x2D, 0x33, 0x65, 0x38,
0x62, 0x2D, 0x62, 0x38, 0x66, 0x32, 0x2D, 0x33, 0x35, 0x38, 0x35, 0x35, 0x61, 0x38, 0x35, 0x36,
0x35, 0x62, 0x36
};
(void)memcpy(in + 67,md5Result,16);
unsigned char base[128] = {00 ,00 ,00 ,01 ,00 ,00 ,00 ,01 ,00 ,00 ,00 ,0x53 ,00 ,00 ,00 ,0x53};
xyshield->GenrateResult(in,base + 16);
char res[128] = {0};
(void)base64_encode(base,0x63,res);
char *new_res = strdup(res);
return new_res;
}
}
//
// Created by jksun on 2021/4/15.
//
#include "base64.h"
#include <stdio.h>
#include <stdlib.h>
/**
* 转解码过程
* 3 * 8 = 4 * 6; 3字节占24位, 4*6=24
* 先将要编码的转成对应的ASCII值
* 如编码: s 1 3
* 对应ASCII值为: 115 49 51
* 对应二进制为: 01110011 00110001 00110011
* 将其6个分组分4组: 011100 110011 000100 110011
* 而计算机是以8bit存储, 所以在每组的高位补两个0如下:
* 00011100 00110011 00000100 00110011对应:28 51 4 51
* 查找base64 转换表 对应 c z E z
*
* 解码
* c z E z
* 对应ASCII值为 99 122 69 122
* 对应表base64_suffix_map的值为 28 51 4 51
* 对应二进制值为 00011100 00110011 00000100 00110011
* 依次去除每组的前两位, 再拼接成3字节
* 即: 01110011 00110001 00110011
* 对应的就是s 1 3
*/
#define BASE64_PAD '='
#define BASE64DE_FIRST '+'
#define BASE64DE_LAST 'z'
/* BASE 64 encode table */
static const char base64en[] = {
'A', 'B', 'C', 'D', 'E', 'F', 'G', 'H',
'I', 'J', 'K', 'L', 'M', 'N', 'O', 'P',
'Q', 'R', 'S', 'T', 'U', 'V', 'W', 'X',
'Y', 'Z', 'a', 'b', 'c', 'd', 'e', 'f',
'g', 'h', 'i', 'j', 'k', 'l', 'm', 'n',
'o', 'p', 'q', 'r', 's', 't', 'u', 'v',
'w', 'x', 'y', 'z', '0', '1', '2', '3',
'4', '5', '6', '7', '8', '9', '+', '/',
};
/* ASCII order for BASE 64 decode, 255 in unused character */
static const unsigned char base64de[] = {
/* nul, soh, stx, etx, eot, enq, ack, bel, */
255, 255, 255, 255, 255, 255, 255, 255,
/* bs, ht, nl, vt, np, cr, so, si, */
255, 255, 255, 255, 255, 255, 255, 255,
/* dle, dc1, dc2, dc3, dc4, nak, syn, etb, */
255, 255, 255, 255, 255, 255, 255, 255,
/* can, em, sub, esc, fs, gs, rs, us, */
255, 255, 255, 255, 255, 255, 255, 255,
/* sp, '!', '"', '#', '$', '%', '&', ''', */
255, 255, 255, 255, 255, 255, 255, 255,
/* '(', ')', '*', '+', ',', '-', '.', '/', */
255, 255, 255, 62, 255, 255, 255, 63,
/* '0', '1', '2', '3', '4', '5', '6', '7', */
52, 53, 54, 55, 56, 57, 58, 59,
/* '8', '9', ':', ';', '<', '=', '>', '?', */
60, 61, 255, 255, 255, 255, 255, 255,
/* '@', 'A', 'B', 'C', 'D', 'E', 'F', 'G', */
255, 0, 1, 2, 3, 4, 5, 6,
/* 'H', 'I', 'J', 'K', 'L', 'M', 'N', 'O', */
7, 8, 9, 10, 11, 12, 13, 14,
/* 'P', 'Q', 'R', 'S', 'T', 'U', 'V', 'W', */
15, 16, 17, 18, 19, 20, 21, 22,
/* 'X', 'Y', 'Z', '[', '\', ']', '^', '_', */
23, 24, 25, 255, 255, 255, 255, 255,
/* '`', 'a', 'b', 'c', 'd', 'e', 'f', 'g', */
255, 26, 27, 28, 29, 30, 31, 32,
/* 'h', 'i', 'j', 'k', 'l', 'm', 'n', 'o', */
33, 34, 35, 36, 37, 38, 39, 40,
/* 'p', 'q', 'r', 's', 't', 'u', 'v', 'w', */
41, 42, 43, 44, 45, 46, 47, 48,
/* 'x', 'y', 'z', '{', '|', '}', '~', del, */
49, 50, 51, 255, 255, 255, 255, 255
};
unsigned int
base64_encode(const unsigned char *in, unsigned int inlen, char *out)
{
int s;
unsigned int i;
unsigned int j;
unsigned char c;
unsigned char l;
s = 0;
l = 0;
for (i = j = 0; i < inlen; i++) {
c = in[i];
switch (s) {
case 0:
s = 1;
out[j++] = base64en[(c >> 2) & 0x3F];
break;
case 1:
s = 2;
out[j++] = base64en[((l & 0x3) << 4) | ((c >> 4) & 0xF)];
break;
case 2:
s = 0;
out[j++] = base64en[((l & 0xF) << 2) | ((c >> 6) & 0x3)];
out[j++] = base64en[c & 0x3F];
break;
}
l = c;
}
switch (s) {
case 1:
out[j++] = base64en[(l & 0x3) << 4];
out[j++] = BASE64_PAD;
out[j++] = BASE64_PAD;
break;
case 2:
out[j++] = base64en[(l & 0xF) << 2];
out[j++] = BASE64_PAD;
break;
}
out[j] = 0;
return j;
}
unsigned int
base64_decode(const char *in, unsigned int inlen, unsigned char *out)
{
unsigned int i;
unsigned int j;
unsigned char c;
if (inlen & 0x3) {
return 0;
}
for (i = j = 0; i < inlen; i++) {
if (in[i] == BASE64_PAD) {
break;
}
if (in[i] < BASE64DE_FIRST || in[i] > BASE64DE_LAST) {
return 0;
}
c = base64de[(unsigned char)in[i]];
if (c == 255) {
return 0;
}
switch (i & 0x3) {
case 0:
out[j] = (c << 2) & 0xFF;
break;
case 1:
out[j++] |= (c >> 4) & 0x3;
out[j] = (c & 0xF) << 4;
break;
case 2:
out[j++] |= (c >> 2) & 0xF;
out[j] = (c & 0x3) << 6;
break;
case 3:
out[j++] |= c;
break;
}
}
return j;
}
//
// Created by smallsun on 2021/4/16.
//
#include "xyAes.h"
unsigned int RCON[10] = {
0x12310000, 0x02000100, 0x04020000, 0x08020200, 0x10102000, 0x30020400, 0x40002000, 0x80002000,
0x1B002000, 0x36200200
};
unsigned int TBox_1[256] = {
0xC66363A5, 0xF87C7C84, 0xEE777799, 0xF67B7B8D, 0xFFF2F20D, 0xD66B6BBD, 0xDE6F6FB1, 0x91C5C554,
0x60303050, 0x02010103, 0xCE6767A9, 0x562B2B7D, 0xE7FEFE19, 0xB5D7D762, 0x4DABABE6, 0xEC76769A,
0x8FCACA45, 0x1F82829D, 0x89C9C940, 0xFA7D7D87, 0xEFFAFA15, 0xB25959EB, 0x8E4747C9, 0xFBF0F00B,
0x41ADADEC, 0xB3D4D467, 0x5FA2A2FD, 0x45AFAFEA, 0x239C9CBF, 0x53A4A4F7, 0xE4727296, 0x9BC0C05B,
0x75B7B7C2, 0xE1FDFD1C, 0x3D9393AE, 0x4C26266A, 0x6C36365A, 0x7E3F3F41, 0xF5F7F702, 0x83CCCC4F,
0x6834345C, 0x51A5A5F4, 0xD1E5E534, 0xF9F1F108, 0xE2717193, 0xABD8D873, 0x62313153, 0x2A15153F,
0x0804040C, 0x95C7C752, 0x46232365, 0x9DC3C35E, 0x30181828, 0x379696A1, 0x0A05050F, 0x2F9A9AB5,
0x0E070709, 0x24121236, 0x1B80809B, 0xDFE2E23D, 0xCDEBEB26, 0x4E272769, 0x7FB2B2CD, 0xEA75759F,
0x1209091B, 0x1D83839E, 0x582C2C74, 0x341A1A2E, 0x361B1B2D, 0xDC6E6EB2, 0xB45A5AEE, 0x5BA0A0FB,
0xA45252F6, 0x763B3B4D, 0xB7D6D661, 0x7DB3B3CE, 0x5229297B, 0xDDE3E33E, 0x5E2F2F71, 0x13848497,
0xA65353F5, 0xB9D1D168, 0x00000000, 0xC1EDED2C, 0x40202060, 0xE3FCFC1F, 0x79B1B1C8, 0xB65B5BED,
0xD46A6ABE, 0x8DCBCB46, 0x67BEBED9, 0x7239394B, 0x944A4ADE, 0x984C4CD4, 0xB05858E8, 0x85CFCF4A,
0xBBD0D06B, 0xC5EFEF2A, 0x4FAAAAE5, 0xEDFBFB16, 0x864343C5, 0x9A4D4DD7, 0x66333355, 0x11858594,
0x8A4545CF, 0xE9F9F910, 0x04020206, 0xFE7F7F81, 0xA05050F0, 0x783C3C44, 0x259F9FBA, 0x4BA8A8E3,
0xA25151F3, 0x5DA3A3FE, 0x804040C0, 0x058F8F8A, 0x3F9292AD, 0x219D9DBC, 0x70383848, 0xF1F5F504,
0x63BCBCDF, 0x77B6B6C1, 0xAFDADA75, 0x42212163, 0x20101030, 0xE5FFFF1A, 0xFDF3F30E, 0xBFD2D26D,
0x81CDCD4C, 0x180C0C14, 0x26131335, 0xC3ECEC2F, 0xBE5F5FE1, 0x359797A2, 0x884444CC, 0x2E171739,
0x93C4C457, 0x55A7A7F2, 0xFC7E7E82, 0x7A3D3D47, 0xC86464AC, 0xBA5D5DE7, 0x3219192B, 0xE6737395,
0xC06060A0, 0x19818198, 0x9E4F4FD1, 0xA3DCDC7F, 0x44222266, 0x542A2A7E, 0x3B9090AB, 0x0B888883,
0x8C4646CA, 0xC7EEEE29, 0x6BB8B8D3, 0x2814143C, 0xA7DEDE79, 0xBC5E5EE2, 0x160B0B1D, 0xADDBDB76,
0xDBE0E03B, 0x64323256, 0x743A3A4E, 0x140A0A1E, 0x924949DB, 0x0C06060A, 0x4824246C, 0xB85C5CE4,
0x9FC2C25D, 0xBDD3D36E, 0x43ACACEF, 0xC46262A6, 0x399191A8, 0x319595A4, 0xD3E4E437, 0xF279798B,
0xD5E7E732, 0x8BC8C843, 0x6E373759, 0xDA6D6DB7, 0x018D8D8C, 0xB1D5D564, 0x9C4E4ED2, 0x49A9A9E0,
0xD86C6CB4, 0xAC5656FA, 0xF3F4F407, 0xCFEAEA25, 0xCA6565AF, 0xF47A7A8E, 0x47AEAEE9, 0x10080818,
0x6FBABAD5, 0xF0787888, 0x4A25256F, 0x5C2E2E72, 0x381C1C24, 0x57A6A6F1, 0x73B4B4C7, 0x97C6C651,
0xCBE8E823, 0xA1DDDD7C, 0xE874749C, 0x3E1F1F21, 0x964B4BDD, 0x61BDBDDC, 0x0D8B8B86, 0x0F8A8A85,
0xE0707090, 0x7C3E3E42, 0x71B5B5C4, 0xCC6666AA, 0x904848D8, 0x06030305, 0xF7F6F601, 0x1C0E0E12,
0xC26161A3, 0x6A35355F, 0xAE5757F9, 0x69B9B9D0, 0x17868691, 0x99C1C158, 0x3A1D1D27, 0x279E9EB9,
0xD9E1E138, 0xEBF8F813, 0x2B9898B3, 0x22111133, 0xD26969BB, 0xA9D9D970, 0x078E8E89, 0x339494A7,
0x2D9B9BB6, 0x3C1E1E22, 0x15878792, 0xC9E9E920, 0x87CECE49, 0xAA5555FF, 0x50282878, 0xA5DFDF7A,
0x038C8C8F, 0x59A1A1F8, 0x09898980, 0x1A0D0D17, 0x65BFBFDA, 0xD7E6E631, 0x844242C6, 0xD06868B8,
0x824141C3, 0x299999B0, 0x5A2D2D77, 0x1E0F0F11, 0x7BB0B0CB, 0xA85454FC, 0x6DBBBBD6, 0x2C16163A
};
unsigned char TBox_2[1024] = {
0x63, 0x63, 0xC6, 0xA5, 0x7C, 0x7C, 0xF8, 0x84, 0x77, 0x77, 0xEE, 0x99, 0x7B, 0x7B, 0xF6, 0x8D,
0xF2, 0xF2, 0xFF, 0x0D, 0x6B, 0x6B, 0xD6, 0xBD, 0x6F, 0x6F, 0xDE, 0xB1, 0xC5, 0xC5, 0x91, 0x54,
0x30, 0x30, 0x60, 0x50, 0x01, 0x01, 0x02, 0x03, 0x67, 0x67, 0xCE, 0xA9, 0x2B, 0x2B, 0x56, 0x7D,
0xFE, 0xFE, 0xE7, 0x19, 0xD7, 0xD7, 0xB5, 0x62, 0xAB, 0xAB, 0x4D, 0xE6, 0x76, 0x76, 0xEC, 0x9A,
0xCA, 0xCA, 0x8F, 0x45, 0x82, 0x82, 0x1F, 0x9D, 0xC9, 0xC9, 0x89, 0x40, 0x7D, 0x7D, 0xFA, 0x87,
0xFA, 0xFA, 0xEF, 0x15, 0x59, 0x59, 0xB2, 0xEB, 0x47, 0x47, 0x8E, 0xC9, 0xF0, 0xF0, 0xFB, 0x0B,
0xAD, 0xAD, 0x41, 0xEC, 0xD4, 0xD4, 0xB3, 0x67, 0xA2, 0xA2, 0x5F, 0xFD, 0xAF, 0xAF, 0x45, 0xEA,
0x9C, 0x9C, 0x23, 0xBF, 0xA4, 0xA4, 0x53, 0xF7, 0x72, 0x72, 0xE4, 0x96, 0xC0, 0xC0, 0x9B, 0x5B,
0xB7, 0xB7, 0x75, 0xC2, 0xFD, 0xFD, 0xE1, 0x1C, 0x93, 0x93, 0x3D, 0xAE, 0x26, 0x26, 0x4C, 0x6A,
0x36, 0x36, 0x6C, 0x5A, 0x3F, 0x3F, 0x7E, 0x41, 0xF7, 0xF7, 0xF5, 0x02, 0xCC, 0xCC, 0x83, 0x4F,
0x34, 0x34, 0x68, 0x5C, 0xA5, 0xA5, 0x51, 0xF4, 0xE5, 0xE5, 0xD1, 0x34, 0xF1, 0xF1, 0xF9, 0x08,
0x71, 0x71, 0xE2, 0x93, 0xD8, 0xD8, 0xAB, 0x73, 0x31, 0x31, 0x62, 0x53, 0x15, 0x15, 0x2A, 0x3F,
0x04, 0x04, 0x08, 0x0C, 0xC7, 0xC7, 0x95, 0x52, 0x23, 0x23, 0x46, 0x65, 0xC3, 0xC3, 0x9D, 0x5E,
0x18, 0x18, 0x30, 0x28, 0x96, 0x96, 0x37, 0xA1, 0x05, 0x05, 0x0A, 0x0F, 0x9A, 0x9A, 0x2F, 0xB5,
0x07, 0x07, 0x0E, 0x09, 0x12, 0x12, 0x24, 0x36, 0x80, 0x80, 0x1B, 0x9B, 0xE2, 0xE2, 0xDF, 0x3D,
0xEB, 0xEB, 0xCD, 0x26, 0x27, 0x27, 0x4E, 0x69, 0xB2, 0xB2, 0x7F, 0xCD, 0x75, 0x75, 0xEA, 0x9F,
0x09, 0x09, 0x12, 0x1B, 0x83, 0x83, 0x1D, 0x9E, 0x2C, 0x2C, 0x58, 0x74, 0x1A, 0x1A, 0x34, 0x2E,
0x1B, 0x1B, 0x36, 0x2D, 0x6E, 0x6E, 0xDC, 0xB2, 0x5A, 0x5A, 0xB4, 0xEE, 0xA0, 0xA0, 0x5B, 0xFB,
0x52, 0x52, 0xA4, 0xF6, 0x3B, 0x3B, 0x76, 0x4D, 0xD6, 0xD6, 0xB7, 0x61, 0xB3, 0xB3, 0x7D, 0xCE,
0x29, 0x29, 0x52, 0x7B, 0xE3, 0xE3, 0xDD, 0x3E, 0x2F, 0x2F, 0x5E, 0x71, 0x84, 0x84, 0x13, 0x97,
0x53, 0x53, 0xA6, 0xF5, 0xD1, 0xD1, 0xB9, 0x68, 0x00, 0x00, 0x00, 0x00, 0xED, 0xED, 0xC1, 0x2C,
0x20, 0x20, 0x40, 0x60, 0xFC, 0xFC, 0xE3, 0x1F, 0xB1, 0xB1, 0x79, 0xC8, 0x5B, 0x5B, 0xB6, 0xED,
0x6A, 0x6A, 0xD4, 0xBE, 0xCB, 0xCB, 0x8D, 0x46, 0xBE, 0xBE, 0x67, 0xD9, 0x39, 0x39, 0x72, 0x4B,
0x4A, 0x4A, 0x94, 0xDE, 0x4C, 0x4C, 0x98, 0xD4, 0x58, 0x58, 0xB0, 0xE8, 0xCF, 0xCF, 0x85, 0x4A,
0xD0, 0xD0, 0xBB, 0x6B, 0xEF, 0xEF, 0xC5, 0x2A, 0xAA, 0xAA, 0x4F, 0xE5, 0xFB, 0xFB, 0xED, 0x16,
0x43, 0x43, 0x86, 0xC5, 0x4D, 0x4D, 0x9A, 0xD7, 0x33, 0x33, 0x66, 0x55, 0x85, 0x85, 0x11, 0x94,
0x45, 0x45, 0x8A, 0xCF, 0xF9, 0xF9, 0xE9, 0x10, 0x02, 0x02, 0x04, 0x06, 0x7F, 0x7F, 0xFE, 0x81,
0x50, 0x50, 0xA0, 0xF0, 0x3C, 0x3C, 0x78, 0x44, 0x9F, 0x9F, 0x25, 0xBA, 0xA8, 0xA8, 0x4B, 0xE3,
0x51, 0x51, 0xA2, 0xF3, 0xA3, 0xA3, 0x5D, 0xFE, 0x40, 0x40, 0x80, 0xC0, 0x8F, 0x8F, 0x05, 0x8A,
0x92, 0x92, 0x3F, 0xAD, 0x9D, 0x9D, 0x21, 0xBC, 0x38, 0x38, 0x70, 0x48, 0xF5, 0xF5, 0xF1, 0x04,
0xBC, 0xBC, 0x63, 0xDF, 0xB6, 0xB6, 0x77, 0xC1, 0xDA, 0xDA, 0xAF, 0x75, 0x21, 0x21, 0x42, 0x63,
0x10, 0x10, 0x20, 0x30, 0xFF, 0xFF, 0xE5, 0x1A, 0xF3, 0xF3, 0xFD, 0x0E, 0xD2, 0xD2, 0xBF, 0x6D,
0xCD, 0xCD, 0x81, 0x4C, 0x0C, 0x0C, 0x18, 0x14, 0x13, 0x13, 0x26, 0x35, 0xEC, 0xEC, 0xC3, 0x2F,
0x5F, 0x5F, 0xBE, 0xE1, 0x97, 0x97, 0x35, 0xA2, 0x44, 0x44, 0x88, 0xCC, 0x17, 0x17, 0x2E, 0x39,
0xC4, 0xC4, 0x93, 0x57, 0xA7, 0xA7, 0x55, 0xF2, 0x7E, 0x7E, 0xFC, 0x82, 0x3D, 0x3D, 0x7A, 0x47,
0x64, 0x64, 0xC8, 0xAC, 0x5D, 0x5D, 0xBA, 0xE7, 0x19, 0x19, 0x32, 0x2B, 0x73, 0x73, 0xE6, 0x95,
0x60, 0x60, 0xC0, 0xA0, 0x81, 0x81, 0x19, 0x98, 0x4F, 0x4F, 0x9E, 0xD1, 0xDC, 0xDC, 0xA3, 0x7F,
0x22, 0x22, 0x44, 0x66, 0x2A, 0x2A, 0x54, 0x7E, 0x90, 0x90, 0x3B, 0xAB, 0x88, 0x88, 0x0B, 0x83,
0x46, 0x46, 0x8C, 0xCA, 0xEE, 0xEE, 0xC7, 0x29, 0xB8, 0xB8, 0x6B, 0xD3, 0x14, 0x14, 0x28, 0x3C,
0xDE, 0xDE, 0xA7, 0x79, 0x5E, 0x5E, 0xBC, 0xE2, 0x0B, 0x0B, 0x16, 0x1D, 0xDB, 0xDB, 0xAD, 0x76,
0xE0, 0xE0, 0xDB, 0x3B, 0x32, 0x32, 0x64, 0x56, 0x3A, 0x3A, 0x74, 0x4E, 0x0A, 0x0A, 0x14, 0x1E,
0x49, 0x49, 0x92, 0xDB, 0x06, 0x06, 0x0C, 0x0A, 0x24, 0x24, 0x48, 0x6C, 0x5C, 0x5C, 0xB8, 0xE4,
0xC2, 0xC2, 0x9F, 0x5D, 0xD3, 0xD3, 0xBD, 0x6E, 0xAC, 0xAC, 0x43, 0xEF, 0x62, 0x62, 0xC4, 0xA6,
0x91, 0x91, 0x39, 0xA8, 0x95, 0x95, 0x31, 0xA4, 0xE4, 0xE4, 0xD3, 0x37, 0x79, 0x79, 0xF2, 0x8B,
0xE7, 0xE7, 0xD5, 0x32, 0xC8, 0xC8, 0x8B, 0x43, 0x37, 0x37, 0x6E, 0x59, 0x6D, 0x6D, 0xDA, 0xB7,
0x8D, 0x8D, 0x01, 0x8C, 0xD5, 0xD5, 0xB1, 0x64, 0x4E, 0x4E, 0x9C, 0xD2, 0xA9, 0xA9, 0x49, 0xE0,
0x6C, 0x6C, 0xD8, 0xB4, 0x56, 0x56, 0xAC, 0xFA, 0xF4, 0xF4, 0xF3, 0x07, 0xEA, 0xEA, 0xCF, 0x25,
0x65, 0x65, 0xCA, 0xAF, 0x7A, 0x7A, 0xF4, 0x8E, 0xAE, 0xAE, 0x47, 0xE9, 0x08, 0x08, 0x10, 0x18,
0xBA, 0xBA, 0x6F, 0xD5, 0x78, 0x78, 0xF0, 0x88, 0x25, 0x25, 0x4A, 0x6F, 0x2E, 0x2E, 0x5C, 0x72,
0x1C, 0x1C, 0x38, 0x24, 0xA6, 0xA6, 0x57, 0xF1, 0xB4, 0xB4, 0x73, 0xC7, 0xC6, 0xC6, 0x97, 0x51,
0xE8, 0xE8, 0xCB, 0x23, 0xDD, 0xDD, 0xA1, 0x7C, 0x74, 0x74, 0xE8, 0x9C, 0x1F, 0x1F, 0x3E, 0x21,
0x4B, 0x4B, 0x96, 0xDD, 0xBD, 0xBD, 0x61, 0xDC, 0x8B, 0x8B, 0x0D, 0x86, 0x8A, 0x8A, 0x0F, 0x85,
0x70, 0x70, 0xE0, 0x90, 0x3E, 0x3E, 0x7C, 0x42, 0xB5, 0xB5, 0x71, 0xC4, 0x66, 0x66, 0xCC, 0xAA,
0x48, 0x48, 0x90, 0xD8, 0x03, 0x03, 0x06, 0x05, 0xF6, 0xF6, 0xF7, 0x01, 0x0E, 0x0E, 0x1C, 0x12,
0x61, 0x61, 0xC2, 0xA3, 0x35, 0x35, 0x6A, 0x5F, 0x57, 0x57, 0xAE, 0xF9, 0xB9, 0xB9, 0x69, 0xD0,
0x86, 0x86, 0x17, 0x91, 0xC1, 0xC1, 0x99, 0x58, 0x1D, 0x1D, 0x3A, 0x27, 0x9E, 0x9E, 0x27, 0xB9,
0xE1, 0xE1, 0xD9, 0x38, 0xF8, 0xF8, 0xEB, 0x13, 0x98, 0x98, 0x2B, 0xB3, 0x11, 0x11, 0x22, 0x33,
0x69, 0x69, 0xD2, 0xBB, 0xD9, 0xD9, 0xA9, 0x70, 0x8E, 0x8E, 0x07, 0x89, 0x94, 0x94, 0x33, 0xA7,
0x9B, 0x9B, 0x2D, 0xB6, 0x1E, 0x1E, 0x3C, 0x22, 0x87, 0x87, 0x15, 0x92, 0xE9, 0xE9, 0xC9, 0x20,
0xCE, 0xCE, 0x87, 0x49, 0x55, 0x55, 0xAA, 0xFF, 0x28, 0x28, 0x50, 0x78, 0xDF, 0xDF, 0xA5, 0x7A,
0x8C, 0x8C, 0x03, 0x8F, 0xA1, 0xA1, 0x59, 0xF8, 0x89, 0x89, 0x09, 0x80, 0x0D, 0x0D, 0x1A, 0x17,
0xBF, 0xBF, 0x65, 0xDA, 0xE6, 0xE6, 0xD7, 0x31, 0x42, 0x42, 0x84, 0xC6, 0x68, 0x68, 0xD0, 0xB8,
0x41, 0x41, 0x82, 0xC3, 0x99, 0x99, 0x29, 0xB0, 0x2D, 0x2D, 0x5A, 0x77, 0x0F, 0x0F, 0x1E, 0x11,
0xB0, 0xB0, 0x7B, 0xCB, 0x54, 0x54, 0xA8, 0xFC, 0xBB, 0xBB, 0x6D, 0xD6, 0x16, 0x16, 0x2C, 0x3A
};
unsigned int TBox_3[256] = {
0x63A5C663, 0x7C84F87C, 0x7799EE77, 0x7B8DF67B, 0xF20DFFF2, 0x6BBDD66B, 0x6FB1DE6F, 0xC55491C5,
0x30506030, 0x01030201, 0x67A9CE67, 0x2B7D562B, 0xFE19E7FE, 0xD762B5D7, 0xABE64DAB, 0x769AEC76,
0xCA458FCA, 0x829D1F82, 0xC94089C9, 0x7D87FA7D, 0xFA15EFFA, 0x59EBB259, 0x47C98E47, 0xF00BFBF0,
0xADEC41AD, 0xD467B3D4, 0xA2FD5FA2, 0xAFEA45AF, 0x9CBF239C, 0xA4F753A4, 0x7296E472, 0xC05B9BC0,
0xB7C275B7, 0xFD1CE1FD, 0x93AE3D93, 0x266A4C26, 0x365A6C36, 0x3F417E3F, 0xF702F5F7, 0xCC4F83CC,
0x345C6834, 0xA5F451A5, 0xE534D1E5, 0xF108F9F1, 0x7193E271, 0xD873ABD8, 0x31536231, 0x153F2A15,
0x040C0804, 0xC75295C7, 0x23654623, 0xC35E9DC3, 0x18283018, 0x96A13796, 0x050F0A05, 0x9AB52F9A,
0x07090E07, 0x12362412, 0x809B1B80, 0xE23DDFE2, 0xEB26CDEB, 0x27694E27, 0xB2CD7FB2, 0x759FEA75,
0x091B1209, 0x839E1D83, 0x2C74582C, 0x1A2E341A, 0x1B2D361B, 0x6EB2DC6E, 0x5AEEB45A, 0xA0FB5BA0,
0x52F6A452, 0x3B4D763B, 0xD661B7D6, 0xB3CE7DB3, 0x297B5229, 0xE33EDDE3, 0x2F715E2F, 0x84971384,
0x53F5A653, 0xD168B9D1, 0x00000000, 0xED2CC1ED, 0x20604020, 0xFC1FE3FC, 0xB1C879B1, 0x5BEDB65B,
0x6ABED46A, 0xCB468DCB, 0xBED967BE, 0x394B7239, 0x4ADE944A, 0x4CD4984C, 0x58E8B058, 0xCF4A85CF,
0xD06BBBD0, 0xEF2AC5EF, 0xAAE54FAA, 0xFB16EDFB, 0x43C58643, 0x4DD79A4D, 0x33556633, 0x85941185,
0x45CF8A45, 0xF910E9F9, 0x02060402, 0x7F81FE7F, 0x50F0A050, 0x3C44783C, 0x9FBA259F, 0xA8E34BA8,
0x51F3A251, 0xA3FE5DA3, 0x40C08040, 0x8F8A058F, 0x92AD3F92, 0x9DBC219D, 0x38487038, 0xF504F1F5,
0xBCDF63BC, 0xB6C177B6, 0xDA75AFDA, 0x21634221, 0x10302010, 0xFF1AE5FF, 0xF30EFDF3, 0xD26DBFD2,
0xCD4C81CD, 0x0C14180C, 0x13352613, 0xEC2FC3EC, 0x5FE1BE5F, 0x97A23597, 0x44CC8844, 0x17392E17,
0xC45793C4, 0xA7F255A7, 0x7E82FC7E, 0x3D477A3D, 0x64ACC864, 0x5DE7BA5D, 0x192B3219, 0x7395E673,
0x60A0C060, 0x81981981, 0x4FD19E4F, 0xDC7FA3DC, 0x22664422, 0x2A7E542A, 0x90AB3B90, 0x88830B88,
0x46CA8C46, 0xEE29C7EE, 0xB8D36BB8, 0x143C2814, 0xDE79A7DE, 0x5EE2BC5E, 0x0B1D160B, 0xDB76ADDB,
0xE03BDBE0, 0x32566432, 0x3A4E743A, 0x0A1E140A, 0x49DB9249, 0x060A0C06, 0x246C4824, 0x5CE4B85C,
0xC25D9FC2, 0xD36EBDD3, 0xACEF43AC, 0x62A6C462, 0x91A83991, 0x95A43195, 0xE437D3E4, 0x798BF279,
0xE732D5E7, 0xC8438BC8, 0x37596E37, 0x6DB7DA6D, 0x8D8C018D, 0xD564B1D5, 0x4ED29C4E, 0xA9E049A9,
0x6CB4D86C, 0x56FAAC56, 0xF407F3F4, 0xEA25CFEA, 0x65AFCA65, 0x7A8EF47A, 0xAEE947AE, 0x08181008,
0xBAD56FBA, 0x7888F078, 0x256F4A25, 0x2E725C2E, 0x1C24381C, 0xA6F157A6, 0xB4C773B4, 0xC65197C6,
0xE823CBE8, 0xDD7CA1DD, 0x749CE874, 0x1F213E1F, 0x4BDD964B, 0xBDDC61BD, 0x8B860D8B, 0x8A850F8A,
0x7090E070, 0x3E427C3E, 0xB5C471B5, 0x66AACC66, 0x48D89048, 0x03050603, 0xF601F7F6, 0x0E121C0E,
0x61A3C261, 0x355F6A35, 0x57F9AE57, 0xB9D069B9, 0x86911786, 0xC15899C1, 0x1D273A1D, 0x9EB9279E,
0xE138D9E1, 0xF813EBF8, 0x98B32B98, 0x11332211, 0x69BBD269, 0xD970A9D9, 0x8E89078E, 0x94A73394,
0x9BB62D9B, 0x1E223C1E, 0x87921587, 0xE920C9E9, 0xCE4987CE, 0x55FFAA55, 0x28785028, 0xDF7AA5DF,
0x8C8F038C, 0xA1F859A1, 0x89800989, 0x0D171A0D, 0xBFDA65BF, 0xE631D7E6, 0x42C68442, 0x68B8D068,
0x41C38241, 0x99B02999, 0x2D775A2D, 0x0F111E0F, 0xB0CB7BB0, 0x54FCA854, 0xBBD66DBB, 0x163A2C16
};
unsigned int TBox_4[256] = {
0x6363A5C6, 0x7C7C84F8, 0x777799EE, 0x7B7B8DF6, 0xF2F20DFF, 0x6B6BBDD6, 0x6F6FB1DE, 0xC5C55491,
0x30305060, 0x01010302, 0x6767A9CE, 0x2B2B7D56, 0xFEFE19E7, 0xD7D762B5, 0xABABE64D, 0x76769AEC,
0xCACA458F, 0x82829D1F, 0xC9C94089, 0x7D7D87FA, 0xFAFA15EF, 0x5959EBB2, 0x4747C98E, 0xF0F00BFB,
0xADADEC41, 0xD4D467B3, 0xA2A2FD5F, 0xAFAFEA45, 0x9C9CBF23, 0xA4A4F753, 0x727296E4, 0xC0C05B9B,
0xB7B7C275, 0xFDFD1CE1, 0x9393AE3D, 0x26266A4C, 0x36365A6C, 0x3F3F417E, 0xF7F702F5, 0xCCCC4F83,
0x34345C68, 0xA5A5F451, 0xE5E534D1, 0xF1F108F9, 0x717193E2, 0xD8D873AB, 0x31315362, 0x15153F2A,
0x04040C08, 0xC7C75295, 0x23236546, 0xC3C35E9D, 0x18182830, 0x9696A137, 0x05050F0A, 0x9A9AB52F,
0x0707090E, 0x12123624, 0x80809B1B, 0xE2E23DDF, 0xEBEB26CD, 0x2727694E, 0xB2B2CD7F, 0x75759FEA,
0x09091B12, 0x83839E1D, 0x2C2C7458, 0x1A1A2E34, 0x1B1B2D36, 0x6E6EB2DC, 0x5A5AEEB4, 0xA0A0FB5B,
0x5252F6A4, 0x3B3B4D76, 0xD6D661B7, 0xB3B3CE7D, 0x29297B52, 0xE3E33EDD, 0x2F2F715E, 0x84849713,
0x5353F5A6, 0xD1D168B9, 0x00000000, 0xEDED2CC1, 0x20206040, 0xFCFC1FE3, 0xB1B1C879, 0x5B5BEDB6,
0x6A6ABED4, 0xCBCB468D, 0xBEBED967, 0x39394B72, 0x4A4ADE94, 0x4C4CD498, 0x5858E8B0, 0xCFCF4A85,
0xD0D06BBB, 0xEFEF2AC5, 0xAAAAE54F, 0xFBFB16ED, 0x4343C586, 0x4D4DD79A, 0x33335566, 0x85859411,
0x4545CF8A, 0xF9F910E9, 0x02020604, 0x7F7F81FE, 0x5050F0A0, 0x3C3C4478, 0x9F9FBA25, 0xA8A8E34B,
0x5151F3A2, 0xA3A3FE5D, 0x4040C080, 0x8F8F8A05, 0x9292AD3F, 0x9D9DBC21, 0x38384870, 0xF5F504F1,
0xBCBCDF63, 0xB6B6C177, 0xDADA75AF, 0x21216342, 0x10103020, 0xFFFF1AE5, 0xF3F30EFD, 0xD2D26DBF,
0xCDCD4C81, 0x0C0C1418, 0x13133526, 0xECEC2FC3, 0x5F5FE1BE, 0x9797A235, 0x4444CC88, 0x1717392E,
0xC4C45793, 0xA7A7F255, 0x7E7E82FC, 0x3D3D477A, 0x6464ACC8, 0x5D5DE7BA, 0x19192B32, 0x737395E6,
0x6060A0C0, 0x81819819, 0x4F4FD19E, 0xDCDC7FA3, 0x22226644, 0x2A2A7E54, 0x9090AB3B, 0x8888830B,
0x4646CA8C, 0xEEEE29C7, 0xB8B8D36B, 0x14143C28, 0xDEDE79A7, 0x5E5EE2BC, 0x0B0B1D16, 0xDBDB76AD,
0xE0E03BDB, 0x32325664, 0x3A3A4E74, 0x0A0A1E14, 0x4949DB92, 0x06060A0C, 0x24246C48, 0x5C5CE4B8,
0xC2C25D9F, 0xD3D36EBD, 0xACACEF43, 0x6262A6C4, 0x9191A839, 0x9595A431, 0xE4E437D3, 0x79798BF2,
0xE7E732D5, 0xC8C8438B, 0x3737596E, 0x6D6DB7DA, 0x8D8D8C01, 0xD5D564B1, 0x4E4ED29C, 0xA9A9E049,
0x6C6CB4D8, 0x5656FAAC, 0xF4F407F3, 0xEAEA25CF, 0x6565AFCA, 0x7A7A8EF4, 0xAEAEE947, 0x08081810,
0xBABAD56F, 0x787888F0, 0x25256F4A, 0x2E2E725C, 0x1C1C2438, 0xA6A6F157, 0xB4B4C773, 0xC6C65197,
0xE8E823CB, 0xDDDD7CA1, 0x74749CE8, 0x1F1F213E, 0x4B4BDD96, 0xBDBDDC61, 0x8B8B860D, 0x8A8A850F,
0x707090E0, 0x3E3E427C, 0xB5B5C471, 0x6666AACC, 0x4848D890, 0x03030506, 0xF6F601F7, 0x0E0E121C,
0x6161A3C2, 0x35355F6A, 0x5757F9AE, 0xB9B9D069, 0x86869117, 0xC1C15899, 0x1D1D273A, 0x9E9EB927,
0xE1E138D9, 0xF8F813EB, 0x9898B32B, 0x11113322, 0x6969BBD2, 0xD9D970A9, 0x8E8E8907, 0x9494A733,
0x9B9BB62D, 0x1E1E223C, 0x87879215, 0xE9E920C9, 0xCECE4987, 0x5555FFAA, 0x28287850, 0xDFDF7AA5,
0x8C8C8F03, 0xA1A1F859, 0x89898009, 0x0D0D171A, 0xBFBFDA65, 0xE6E631D7, 0x4242C684, 0x6868B8D0,
0x4141C382, 0x9999B029, 0x2D2D775A, 0x0F0F111E, 0xB0B0CB7B, 0x5454FCA8, 0xBBBBD66D, 0x16163A2C
};
unsigned int TBox_5[256] = {
0x51F4A750, 0x7E416553, 0x1A17A4C3, 0x3A275E96, 0x3BAB6BCB, 0x1F9D45F1, 0xACFA58AB, 0x4BE30393,
0x2030FA55, 0xAD766DF6, 0x88CC7691, 0xF5024C25, 0x4FE5D7FC, 0xC52ACBD7, 0x26354480, 0xB562A38F,
0xDEB15A49, 0x25BA1B67, 0x45EA0E98, 0x5DFEC0E1, 0xC32F7502, 0x814CF012, 0x8D4697A3, 0x6BD3F9C6,
0x038F5FE7, 0x15929C95, 0xBF6D7AEB, 0x955259DA, 0xD4BE832D, 0x587421D3, 0x49E06929, 0x8EC9C844,
0x75C2896A, 0xF48E7978, 0x99583E6B, 0x27B971DD, 0xBEE14FB6, 0xF088AD17, 0xC920AC66, 0x7DCE3AB4,
0x63DF4A18, 0xE51A3182, 0x97513360, 0x62537F45, 0xB16477E0, 0xBB6BAE84, 0xFE81A01C, 0xF9082B94,
0x70486858, 0x8F45FD19, 0x94DE6C87, 0x527BF8B7, 0xAB73D323, 0x724B02E2, 0xE31F8F57, 0x6655AB2A,
0xB2EB2807, 0x2FB5C203, 0x86C57B9A, 0xD33708A5, 0x302887F2, 0x23BFA5B2, 0x02036ABA, 0xED16825C,
0x8ACF1C2B, 0xA779B492, 0xF307F2F0, 0x4E69E2A1, 0x65DAF4CD, 0x0605BED5, 0xD134621F, 0xC4A6FE8A,
0x342E539D, 0xA2F355A0, 0x058AE132, 0xA4F6EB75, 0x0B83EC39, 0x4060EFAA, 0x5E719F06, 0xBD6E1051,
0x3E218AF9, 0x96DD063D, 0xDD3E05AE, 0x4DE6BD46, 0x91548DB5, 0x71C45D05, 0x0406D46F, 0x605015FF,
0x1998FB24, 0xD6BDE997, 0x894043CC, 0x67D99E77, 0xB0E842BD, 0x07898B88, 0xE7195B38, 0x79C8EEDB,
0xA17C0A47, 0x7C420FE9, 0xF8841EC9, 0x00000000, 0x09808683, 0x322BED48, 0x1E1170AC, 0x6C5A724E,
0xFD0EFFFB, 0x0F853856, 0x3DAED51E, 0x362D3927, 0x0A0FD964, 0x685CA621, 0x9B5B54D1, 0x24362E3A,
0x0C0A67B1, 0x9357E70F, 0xB4EE96D2, 0x1B9B919E, 0x80C0C54F, 0x61DC20A2, 0x5A774B69, 0x1C121A16,
0xE293BA0A, 0xC0A02AE5, 0x3C22E043, 0x121B171D, 0x0E090D0B, 0xF28BC7AD, 0x2DB6A8B9, 0x141EA9C8,
0x57F11985, 0xAF75074C, 0xEE99DDBB, 0xA37F60FD, 0xF701269F, 0x5C72F5BC, 0x44663BC5, 0x5BFB7E34,
0x8B432976, 0xCB23C6DC, 0xB6EDFC68, 0xB8E4F163, 0xD731DCCA, 0x42638510, 0x13972240, 0x84C61120,
0x854A247D, 0xD2BB3DF8, 0xAEF93211, 0xC729A16D, 0x1D9E2F4B, 0xDCB230F3, 0x0D8652EC, 0x77C1E3D0,
0x2BB3166C, 0xA970B999, 0x119448FA, 0x47E96422, 0xA8FC8CC4, 0xA0F03F1A, 0x567D2CD8, 0x223390EF,
0x87494EC7, 0xD938D1C1, 0x8CCAA2FE, 0x98D40B36, 0xA6F581CF, 0xA57ADE28, 0xDAB78E26, 0x3FADBFA4,
0x2C3A9DE4, 0x5078920D, 0x6A5FCC9B, 0x547E4662, 0xF68D13C2, 0x90D8B8E8, 0x2E39F75E, 0x82C3AFF5,
0x9F5D80BE, 0x69D0937C, 0x6FD52DA9, 0xCF2512B3, 0xC8AC993B, 0x10187DA7, 0xE89C636E, 0xDB3BBB7B,
0xCD267809, 0x6E5918F4, 0xEC9AB701, 0x834F9AA8, 0xE6956E65, 0xAAFFE67E, 0x21BCCF08, 0xEF15E8E6,
0xBAE79BD9, 0x4A6F36CE, 0xEA9F09D4, 0x29B07CD6, 0x31A4B2AF, 0x2A3F2331, 0xC6A59430, 0x35A266C0,
0x744EBC37, 0xFC82CAA6, 0xE090D0B0, 0x33A7D815, 0xF104984A, 0x41ECDAF7, 0x7FCD500E, 0x1791F62F,
0x764DD68D, 0x43EFB04D, 0xCCAA4D54, 0xE49604DF, 0x9ED1B5E3, 0x4C6A881B, 0xC12C1FB8, 0x4665517F,
0x9D5EEA04, 0x018C355D, 0xFA877473, 0xFB0B412E, 0xB3671D5A, 0x92DBD252, 0xE9105633, 0x6DD64713,
0x9AD7618C, 0x37A10C7A, 0x59F8148E, 0xEB133C89, 0xCEA927EE, 0xB761C935, 0xE11CE5ED, 0x7A47B13C,
0x9CD2DF59, 0x55F2733F, 0x1814CE79, 0x73C737BF, 0x53F7CDEA, 0x5FFDAA5B, 0xDF3D6F14, 0x7844DB86,
0xCAAFF381, 0xB968C43E, 0x3824342C, 0xC2A3405F, 0x161DC372, 0xBCE2250C, 0x283C498B, 0xFF0D9541,
0x39A80171, 0x080CB3DE, 0xD8B4E49C, 0x6456C190, 0x7BCB8461, 0xD532B670, 0x486C5C74, 0xD0B85742
};
unsigned int TBox_6[256] = {
0x5051F4A7, 0x537E4165, 0xC31A17A4, 0x963A275E, 0xCB3BAB6B, 0xF11F9D45, 0xABACFA58, 0x934BE303,
0x552030FA, 0xF6AD766D, 0x9188CC76, 0x25F5024C, 0xFC4FE5D7, 0xD7C52ACB, 0x80263544, 0x8FB562A3,
0x49DEB15A, 0x6725BA1B, 0x9845EA0E, 0xE15DFEC0, 0x02C32F75, 0x12814CF0, 0xA38D4697, 0xC66BD3F9,
0xE7038F5F, 0x9515929C, 0xEBBF6D7A, 0xDA955259, 0x2DD4BE83, 0xD3587421, 0x2949E069, 0x448EC9C8,
0x6A75C289, 0x78F48E79, 0x6B99583E, 0xDD27B971, 0xB6BEE14F, 0x17F088AD, 0x66C920AC, 0xB47DCE3A,
0x1863DF4A, 0x82E51A31, 0x60975133, 0x4562537F, 0xE0B16477, 0x84BB6BAE, 0x1CFE81A0, 0x94F9082B,
0x58704868, 0x198F45FD, 0x8794DE6C, 0xB7527BF8, 0x23AB73D3, 0xE2724B02, 0x57E31F8F, 0x2A6655AB,
0x07B2EB28, 0x032FB5C2, 0x9A86C57B, 0xA5D33708, 0xF2302887, 0xB223BFA5, 0xBA02036A, 0x5CED1682,
0x2B8ACF1C, 0x92A779B4, 0xF0F307F2, 0xA14E69E2, 0xCD65DAF4, 0xD50605BE, 0x1FD13462, 0x8AC4A6FE,
0x9D342E53, 0xA0A2F355, 0x32058AE1, 0x75A4F6EB, 0x390B83EC, 0xAA4060EF, 0x065E719F, 0x51BD6E10,
0xF93E218A, 0x3D96DD06, 0xAEDD3E05, 0x464DE6BD, 0xB591548D, 0x0571C45D, 0x6F0406D4, 0xFF605015,
0x241998FB, 0x97D6BDE9, 0xCC894043, 0x7767D99E, 0xBDB0E842, 0x8807898B, 0x38E7195B, 0xDB79C8EE,
0x47A17C0A, 0xE97C420F, 0xC9F8841E, 0x00000000, 0x83098086, 0x48322BED, 0xAC1E1170, 0x4E6C5A72,
0xFBFD0EFF, 0x560F8538, 0x1E3DAED5, 0x27362D39, 0x640A0FD9, 0x21685CA6, 0xD19B5B54, 0x3A24362E,
0xB10C0A67, 0x0F9357E7, 0xD2B4EE96, 0x9E1B9B91, 0x4F80C0C5, 0xA261DC20, 0x695A774B, 0x161C121A,
0x0AE293BA, 0xE5C0A02A, 0x433C22E0, 0x1D121B17, 0x0B0E090D, 0xADF28BC7, 0xB92DB6A8, 0xC8141EA9,
0x8557F119, 0x4CAF7507, 0xBBEE99DD, 0xFDA37F60, 0x9FF70126, 0xBC5C72F5, 0xC544663B, 0x345BFB7E,
0x768B4329, 0xDCCB23C6, 0x68B6EDFC, 0x63B8E4F1, 0xCAD731DC, 0x10426385, 0x40139722, 0x2084C611,
0x7D854A24, 0xF8D2BB3D, 0x11AEF932, 0x6DC729A1, 0x4B1D9E2F, 0xF3DCB230, 0xEC0D8652, 0xD077C1E3,
0x6C2BB316, 0x99A970B9, 0xFA119448, 0x2247E964, 0xC4A8FC8C, 0x1AA0F03F, 0xD8567D2C, 0xEF223390,
0xC787494E, 0xC1D938D1, 0xFE8CCAA2, 0x3698D40B, 0xCFA6F581, 0x28A57ADE, 0x26DAB78E, 0xA43FADBF,
0xE42C3A9D, 0x0D507892, 0x9B6A5FCC, 0x62547E46, 0xC2F68D13, 0xE890D8B8, 0x5E2E39F7, 0xF582C3AF,
0xBE9F5D80, 0x7C69D093, 0xA96FD52D, 0xB3CF2512, 0x3BC8AC99, 0xA710187D, 0x6EE89C63, 0x7BDB3BBB,
0x09CD2678, 0xF46E5918, 0x01EC9AB7, 0xA8834F9A, 0x65E6956E, 0x7EAAFFE6, 0x0821BCCF, 0xE6EF15E8,
0xD9BAE79B, 0xCE4A6F36, 0xD4EA9F09, 0xD629B07C, 0xAF31A4B2, 0x312A3F23, 0x30C6A594, 0xC035A266,
0x37744EBC, 0xA6FC82CA, 0xB0E090D0, 0x1533A7D8, 0x4AF10498, 0xF741ECDA, 0x0E7FCD50, 0x2F1791F6,
0x8D764DD6, 0x4D43EFB0, 0x54CCAA4D, 0xDFE49604, 0xE39ED1B5, 0x1B4C6A88, 0xB8C12C1F, 0x7F466551,
0x049D5EEA, 0x5D018C35, 0x73FA8774, 0x2EFB0B41, 0x5AB3671D, 0x5292DBD2, 0x33E91056, 0x136DD647,
0x8C9AD761, 0x7A37A10C, 0x8E59F814, 0x89EB133C, 0xEECEA927, 0x35B761C9, 0xEDE11CE5, 0x3C7A47B1,
0x599CD2DF, 0x3F55F273, 0x791814CE, 0xBF73C737, 0xEA53F7CD, 0x5B5FFDAA, 0x14DF3D6F, 0x867844DB,
0x81CAAFF3, 0x3EB968C4, 0x2C382434, 0x5FC2A340, 0x72161DC3, 0x0CBCE225, 0x8B283C49, 0x41FF0D95,
0x7139A801, 0xDE080CB3, 0x9CD8B4E4, 0x906456C1, 0x617BCB84, 0x70D532B6, 0x74486C5C, 0x42D0B857
};
unsigned int TBox_7[256] = {
0xA75051F4, 0x65537E41, 0xA4C31A17, 0x5E963A27, 0x6BCB3BAB, 0x45F11F9D, 0x58ABACFA, 0x03934BE3,
0xFA552030, 0x6DF6AD76, 0x769188CC, 0x4C25F502, 0xD7FC4FE5, 0xCBD7C52A, 0x44802635, 0xA38FB562,
0x5A49DEB1, 0x1B6725BA, 0x0E9845EA, 0xC0E15DFE, 0x7502C32F, 0xF012814C, 0x97A38D46, 0xF9C66BD3,
0x5FE7038F, 0x9C951592, 0x7AEBBF6D, 0x59DA9552, 0x832DD4BE, 0x21D35874, 0x692949E0, 0xC8448EC9,
0x896A75C2, 0x7978F48E, 0x3E6B9958, 0x71DD27B9, 0x4FB6BEE1, 0xAD17F088, 0xAC66C920, 0x3AB47DCE,
0x4A1863DF, 0x3182E51A, 0x33609751, 0x7F456253, 0x77E0B164, 0xAE84BB6B, 0xA01CFE81, 0x2B94F908,
0x68587048, 0xFD198F45, 0x6C8794DE, 0xF8B7527B, 0xD323AB73, 0x02E2724B, 0x8F57E31F, 0xAB2A6655,
0x2807B2EB, 0xC2032FB5, 0x7B9A86C5, 0x08A5D337, 0x87F23028, 0xA5B223BF, 0x6ABA0203, 0x825CED16,
0x1C2B8ACF, 0xB492A779, 0xF2F0F307, 0xE2A14E69, 0xF4CD65DA, 0xBED50605, 0x621FD134, 0xFE8AC4A6,
0x539D342E, 0x55A0A2F3, 0xE132058A, 0xEB75A4F6, 0xEC390B83, 0xEFAA4060, 0x9F065E71, 0x1051BD6E,
0x8AF93E21, 0x063D96DD, 0x05AEDD3E, 0xBD464DE6, 0x8DB59154, 0x5D0571C4, 0xD46F0406, 0x15FF6050,
0xFB241998, 0xE997D6BD, 0x43CC8940, 0x9E7767D9, 0x42BDB0E8, 0x8B880789, 0x5B38E719, 0xEEDB79C8,
0x0A47A17C, 0x0FE97C42, 0x1EC9F884, 0x00000000, 0x86830980, 0xED48322B, 0x70AC1E11, 0x724E6C5A,
0xFFFBFD0E, 0x38560F85, 0xD51E3DAE, 0x3927362D, 0xD9640A0F, 0xA621685C, 0x54D19B5B, 0x2E3A2436,
0x67B10C0A, 0xE70F9357, 0x96D2B4EE, 0x919E1B9B, 0xC54F80C0, 0x20A261DC, 0x4B695A77, 0x1A161C12,
0xBA0AE293, 0x2AE5C0A0, 0xE0433C22, 0x171D121B, 0x0D0B0E09, 0xC7ADF28B, 0xA8B92DB6, 0xA9C8141E,
0x198557F1, 0x074CAF75, 0xDDBBEE99, 0x60FDA37F, 0x269FF701, 0xF5BC5C72, 0x3BC54466, 0x7E345BFB,
0x29768B43, 0xC6DCCB23, 0xFC68B6ED, 0xF163B8E4, 0xDCCAD731, 0x85104263, 0x22401397, 0x112084C6,
0x247D854A, 0x3DF8D2BB, 0x3211AEF9, 0xA16DC729, 0x2F4B1D9E, 0x30F3DCB2, 0x52EC0D86, 0xE3D077C1,
0x166C2BB3, 0xB999A970, 0x48FA1194, 0x642247E9, 0x8CC4A8FC, 0x3F1AA0F0, 0x2CD8567D, 0x90EF2233,
0x4EC78749, 0xD1C1D938, 0xA2FE8CCA, 0x0B3698D4, 0x81CFA6F5, 0xDE28A57A, 0x8E26DAB7, 0xBFA43FAD,
0x9DE42C3A, 0x920D5078, 0xCC9B6A5F, 0x4662547E, 0x13C2F68D, 0xB8E890D8, 0xF75E2E39, 0xAFF582C3,
0x80BE9F5D, 0x937C69D0, 0x2DA96FD5, 0x12B3CF25, 0x993BC8AC, 0x7DA71018, 0x636EE89C, 0xBB7BDB3B,
0x7809CD26, 0x18F46E59, 0xB701EC9A, 0x9AA8834F, 0x6E65E695, 0xE67EAAFF, 0xCF0821BC, 0xE8E6EF15,
0x9BD9BAE7, 0x36CE4A6F, 0x09D4EA9F, 0x7CD629B0, 0xB2AF31A4, 0x23312A3F, 0x9430C6A5, 0x66C035A2,
0xBC37744E, 0xCAA6FC82, 0xD0B0E090, 0xD81533A7, 0x984AF104, 0xDAF741EC, 0x500E7FCD, 0xF62F1791,
0xD68D764D, 0xB04D43EF, 0x4D54CCAA, 0x04DFE496, 0xB5E39ED1, 0x881B4C6A, 0x1FB8C12C, 0x517F4665,
0xEA049D5E, 0x355D018C, 0x7473FA87, 0x412EFB0B, 0x1D5AB367, 0xD25292DB, 0x5633E910, 0x47136DD6,
0x618C9AD7, 0x0C7A37A1, 0x148E59F8, 0x3C89EB13, 0x27EECEA9, 0xC935B761, 0xE5EDE11C, 0xB13C7A47,
0xDF599CD2, 0x733F55F2, 0xCE791814, 0x37BF73C7, 0xCDEA53F7, 0xAA5B5FFD, 0x6F14DF3D, 0xDB867844,
0xF381CAAF, 0xC43EB968, 0x342C3824, 0x405FC2A3, 0xC372161D, 0x250CBCE2, 0x498B283C, 0x9541FF0D,
0x017139A8, 0xB3DE080C, 0xE49CD8B4, 0xC1906456, 0x84617BCB, 0xB670D532, 0x5C74486C, 0x5742D0B8
};
unsigned int TBox_8[256] = {
0xF4A75051, 0x4165537E, 0x17A4C31A, 0x275E963A, 0xAB6BCB3B, 0x9D45F11F, 0xFA58ABAC, 0xE303934B,
0x30FA5520, 0x766DF6AD, 0xCC769188, 0x024C25F5, 0xE5D7FC4F, 0x2ACBD7C5, 0x35448026, 0x62A38FB5,
0xB15A49DE, 0xBA1B6725, 0xEA0E9845, 0xFEC0E15D, 0x2F7502C3, 0x4CF01281, 0x4697A38D, 0xD3F9C66B,
0x8F5FE703, 0x929C9515, 0x6D7AEBBF, 0x5259DA95, 0xBE832DD4, 0x7421D358, 0xE0692949, 0xC9C8448E,
0xC2896A75, 0x8E7978F4, 0x583E6B99, 0xB971DD27, 0xE14FB6BE, 0x88AD17F0, 0x20AC66C9, 0xCE3AB47D,
0xDF4A1863, 0x1A3182E5, 0x51336097, 0x537F4562, 0x6477E0B1, 0x6BAE84BB, 0x81A01CFE, 0x082B94F9,
0x48685870, 0x45FD198F, 0xDE6C8794, 0x7BF8B752, 0x73D323AB, 0x4B02E272, 0x1F8F57E3, 0x55AB2A66,
0xEB2807B2, 0xB5C2032F, 0xC57B9A86, 0x3708A5D3, 0x2887F230, 0xBFA5B223, 0x036ABA02, 0x16825CED,
0xCF1C2B8A, 0x79B492A7, 0x07F2F0F3, 0x69E2A14E, 0xDAF4CD65, 0x05BED506, 0x34621FD1, 0xA6FE8AC4,
0x2E539D34, 0xF355A0A2, 0x8AE13205, 0xF6EB75A4, 0x83EC390B, 0x60EFAA40, 0x719F065E, 0x6E1051BD,
0x218AF93E, 0xDD063D96, 0x3E05AEDD, 0xE6BD464D, 0x548DB591, 0xC45D0571, 0x06D46F04, 0x5015FF60,
0x98FB2419, 0xBDE997D6, 0x4043CC89, 0xD99E7767, 0xE842BDB0, 0x898B8807, 0x195B38E7, 0xC8EEDB79,
0x7C0A47A1, 0x420FE97C, 0x841EC9F8, 0x00000000, 0x80868309, 0x2BED4832, 0x1170AC1E, 0x5A724E6C,
0x0EFFFBFD, 0x8538560F, 0xAED51E3D, 0x2D392736, 0x0FD9640A, 0x5CA62168, 0x5B54D19B, 0x362E3A24,
0x0A67B10C, 0x57E70F93, 0xEE96D2B4, 0x9B919E1B, 0xC0C54F80, 0xDC20A261, 0x774B695A, 0x121A161C,
0x93BA0AE2, 0xA02AE5C0, 0x22E0433C, 0x1B171D12, 0x090D0B0E, 0x8BC7ADF2, 0xB6A8B92D, 0x1EA9C814,
0xF1198557, 0x75074CAF, 0x99DDBBEE, 0x7F60FDA3, 0x01269FF7, 0x72F5BC5C, 0x663BC544, 0xFB7E345B,
0x4329768B, 0x23C6DCCB, 0xEDFC68B6, 0xE4F163B8, 0x31DCCAD7, 0x63851042, 0x97224013, 0xC6112084,
0x4A247D85, 0xBB3DF8D2, 0xF93211AE, 0x29A16DC7, 0x9E2F4B1D, 0xB230F3DC, 0x8652EC0D, 0xC1E3D077,
0xB3166C2B, 0x70B999A9, 0x9448FA11, 0xE9642247, 0xFC8CC4A8, 0xF03F1AA0, 0x7D2CD856, 0x3390EF22,
0x494EC787, 0x38D1C1D9, 0xCAA2FE8C, 0xD40B3698, 0xF581CFA6, 0x7ADE28A5, 0xB78E26DA, 0xADBFA43F,
0x3A9DE42C, 0x78920D50, 0x5FCC9B6A, 0x7E466254, 0x8D13C2F6, 0xD8B8E890, 0x39F75E2E, 0xC3AFF582,
0x5D80BE9F, 0xD0937C69, 0xD52DA96F, 0x2512B3CF, 0xAC993BC8, 0x187DA710, 0x9C636EE8, 0x3BBB7BDB,
0x267809CD, 0x5918F46E, 0x9AB701EC, 0x4F9AA883, 0x956E65E6, 0xFFE67EAA, 0xBCCF0821, 0x15E8E6EF,
0xE79BD9BA, 0x6F36CE4A, 0x9F09D4EA, 0xB07CD629, 0xA4B2AF31, 0x3F23312A, 0xA59430C6, 0xA266C035,
0x4EBC3774, 0x82CAA6FC, 0x90D0B0E0, 0xA7D81533, 0x04984AF1, 0xECDAF741, 0xCD500E7F, 0x91F62F17,
0x4DD68D76, 0xEFB04D43, 0xAA4D54CC, 0x9604DFE4, 0xD1B5E39E, 0x6A881B4C, 0x2C1FB8C1, 0x65517F46,
0x5EEA049D, 0x8C355D01, 0x877473FA, 0x0B412EFB, 0x671D5AB3, 0xDBD25292, 0x105633E9, 0xD647136D,
0xD7618C9A, 0xA10C7A37, 0xF8148E59, 0x133C89EB, 0xA927EECE, 0x61C935B7, 0x1CE5EDE1, 0x47B13C7A,
0xD2DF599C, 0xF2733F55, 0x14CE7918, 0xC737BF73, 0xF7CDEA53, 0xFDAA5B5F, 0x3D6F14DF, 0x44DB8678,
0xAFF381CA, 0x68C43EB9, 0x24342C38, 0xA3405FC2, 0x1DC37216, 0xE2250CBC, 0x3C498B28, 0x0D9541FF,
0xA8017139, 0x0CB3DE08, 0xB4E49CD8, 0x56C19064, 0xCB84617B, 0x32B670D5, 0x6C5C7448, 0xB85742D0
};
unsigned char rsbox[256] = {
0x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB,
0x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB,
0x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E,
0x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25,
0x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92,
0x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84,
0x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06,
0xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B,
0x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73,
0x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E,
0x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B,
0xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4,
0x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F,
0x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF,
0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61,
0x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D
};
typedef unsigned char uint8;
typedef unsigned short uint16;
typedef unsigned long DWORD_PTR;
#define BYTE uint8
#define WORD uint16
#define DWORD unsigned long
#define LOBYTE(w) ((BYTE)(((DWORD_PTR)(w)) & 0xff))
#define HIBYTE(w) ((BYTE)((((DWORD_PTR)(w)) >> 8) & 0xff))
#define BYTEn(x, n) (*((BYTE*)&(x)+n))
#define WORDn(x, n) (*((WORD*)&(x)+n))
#define BYTE0(x) BYTEn(x, 0) // byte 0 (counting from 0) 添加此宏定义
#define BYTE1(x) BYTEn(x, 1) // byte 1 (counting from 0)
#define BYTE2(x) BYTEn(x, 2)
#define BYTE3(x) BYTEn(x, 3)
#define BYTE4(x) BYTEn(x, 4)
//#define __builtin_bswap32(x) \
// ((((x) & 0xff000000u) >> 24) | (((x) & 0x00ff0000u) >> 8) | \
// (((x) & 0x0000ff00u) << 8) | (((x) & 0x000000ffu) << 24))
//#define bswap32(x) ((unsigned int)__builtin_bswap32(x))
#include <stdio.h>
//将一个32位数高低16位交换
unsigned int bswap32(unsigned int v)
{
return ((v & 0xff) << 24) | ((v & 0xff00) << 8) |
((v & 0xff0000) >> 8) | (v >> 24);
}
typedef struct {
unsigned char roundKey[0x100];
int bits;
}XYAES_KEY;
// sub_D37CD27C
int KeyExpansion(const int* key,const int bits,unsigned int* ctx) {
// 处理后结果
// 04 42 B9 C6 1A 24 32 C6 6F 76 37 DC F5 7B 0E C0
// BE A4 A9 7F A4 80 9B B9 CB F6 AC 65 3E 8D A2 A5
// B8 17 F4 47 1C 97 6F FE D7 61 C3 9B E9 EC 61 3E
// 0A 09 38 AC 16 9E 57 52 C1 FF 94 C9 28 13 F5 F7
// 62 3F 47 42 74 A1 10 10 B5 5E 84 D9 9D 4D 71 2E
// 53 41 B4 F1 27 E0 A4 E1 92 BE 20 38 0F F3 51 16
// 14 33 BB 10 33 D3 1F F1 A1 6D 3F C9 AE 9E 6E DF
// 8A F7 B0 CF B9 24 AF 3E 18 49 90 F7 B6 D7 FE 28
// BE 99 BE F4 07 BD 11 CA 1F F4 81 3D A9 23 7F 15
// E7 6A 98 3D E0 D7 89 F7 FF 23 08 CA 56 00 77 DF
// 79 D9 DB FE 99 0E 52 09 66 2D 5A C3 30 2D 2D 1C
// 04 42 b9 c6 1a 24 32 c6 6f 76 37 dc f5 7b 0e c0
// be a4 a9 7f a4 80 9b b9 cb f6 ac 65 3e 8d a2 a5
// b8 17 f4 47 1c 97 6f fe d7 61 c3 9b e9 ec 61 3e
// 0a 09 38 ac 16 9e 57 52 c1 ff 94 c9 28 13 f5 f7
// 62 3f 47 42 74 a1 10 10 b5 5e 84 d9 9d 4d 71 2e
// 53 41 b4 f1 27 e0 a4 e1 92 be 20 38 0f f3 51 16
// 14 33 bb 10 33 d3 1f f1 a1 6d 3f c9 ae 9e 6e df
// 8a f7 b0 cf b9 24 af 3e 18 49 90 f7 b6 d7 fe 28
// be 99 be f4 07 bd 11 ca 1f f4 81 3d a9 23 7f 15
// e7 6a 98 3d e0 d7 89 f7 ff 23 08 ca 56 00 77 df
// 79 d9 db fe 99 0e 52 09 66 2d 5a c3 30 2d 2d 1c
//
int nRet = 0;
if (bits != 128 && bits != 192 && bits != 256) {
return 0;
}
// 设置加密处理轮数
if (bits == 128) {
ctx[60] = 10;
} else if (bits == 192) {
ctx[60] = 12;
} else {
ctx[60] = 14;
}
// 1111 0001 1000 1001 0010 0001 0011 0001
// 0000 0000 0000 0000 0000 0000 1111 1111
// 0000 0000 0000 0000 0000 0000 0011 0001
// 0011 0001
// 1111 1111
// 0011 0001
//04 42 B9 C6 1A 24 32 C6 6F 76 37 DC F5 7B 0E C0
ctx[0] = bswap32(key[0]) ^ 0xF1892131;
ctx[1] = bswap32(key[1]) ^ 0xFF001123;
ctx[2] = bswap32(key[2]) ^ 0xF1001356;
ctx[3] = bswap32(key[3]) ^ 0xF1234890;
if (bits == 128) {
int i = 0;
while (true) {
ctx[4] = (ctx[0] ^ (TBox_3[ctx[3] >> 0x10 & 0xFF] & 0xFF000000)) ^ (TBox_4[ctx[3] >> 8 & 0xFF] & 0xFF0000) ^ (TBox_1[ctx[3] & 0xFF] & 0xFF00) ^ (TBox_2[(ctx[3] >> 0x18 & 0xFF) * 4]) ^ RCON[i];
ctx[5] = ctx[1] ^ ctx[4];
ctx[6] = ctx[2] ^ ctx[5];
ctx[7] = ctx[3] ^ ctx[6];
if (++i == 10) {
break;
}
ctx += 4;
}
nRet = 1;
} else if (bits == 192){
// 192 位
nRet = 1;
} else {
// 256 位
nRet = 1;
}
return nRet;
}
//sub_4B638
int AesInitCtx(const int* key,const int bits,unsigned int* ctx) {
int nRet = KeyExpansion(key,bits,ctx);
if (nRet <= -1) {
return nRet;
}
// 10轮结果
// 79 D9 DB FE 99 0E 52 09 66 2D 5A C3 30 2D 2D 1C
// E7 6A 98 3D E0 D7 89 F7 FF 23 08 CA 56 00 77 DF
// BE 99 BE F4 07 BD 11 CA 1F F4 81 3D A9 23 7F 15
// 8A F7 B0 CF B9 24 AF 3E 18 49 90 F7 B6 D7 FE 28
// 14 33 BB 10 33 D3 1F F1 A1 6D 3F C9 AE 9E 6E DF
// 53 41 B4 F1 27 E0 A4 E1 92 BE 20 38 0F F3 51 16
// 62 3F 47 42 74 A1 10 10 B5 5E 84 D9 9D 4D 71 2E
// 0A 09 38 AC 16 9E 57 52 C1 FF 94 C9 28 13 F5 F7
// B8 17 F4 47 1C 97 6F FE D7 61 C3 9B E9 EC 61 3E
// BE A4 A9 7F A4 80 9B B9 CB F6 AC 65 3E 8D A2 A5
// 04 42 B9 C6 1A 24 32 C6 6F 76 37 DC F5 7B 0E C0
int j = ctx[60];
unsigned int temp = 0;
unsigned int* ctx_temp;
for(int i = 0;i < j; i++,j--) {
ctx_temp = ctx + i * 4;
temp = ctx_temp[0];
ctx_temp[0] = ctx_temp[j * 4 - i * 4];
ctx_temp[j * 4 - i * 4] = temp;
temp = ctx_temp[1];
ctx_temp[1] = ctx_temp[j * 4 + 1 - i * 4];
ctx_temp[j * 4 - i * 4 + 1] = temp;
temp = ctx_temp[2];
ctx_temp[2] = ctx_temp[4 * j + 2 - i * 4];
ctx_temp[j * 4 - i * 4 + 2] = temp;
temp = ctx_temp[3];
ctx_temp[3] = ctx_temp[j * 4 + 3 - i * 4];
ctx_temp[j * 4 - i * 4 + 3] = temp;
}
ctx_temp = ctx;
for (int k = 1; k < ctx[60]; ++k) {
ctx_temp += 4;
ctx_temp[0] = TBox_8[TBox_2[(ctx_temp[0] & 0xFF) * 4]] ^ TBox_5[TBox_2[(ctx_temp[0] >> 0x18) * 4]] ^ TBox_6[TBox_2[((ctx_temp[0] >> 0x10) & 0xFF) * 4]] ^ TBox_7[TBox_2[((ctx_temp[0] >> 0x8) & 0xFF) * 4]];
ctx_temp[1] = TBox_8[TBox_2[(ctx_temp[1] & 0xFF) * 4]] ^ TBox_5[TBox_2[(ctx_temp[1] >> 0x18) * 4]] ^ TBox_6[TBox_2[((ctx_temp[1] >> 0x10) & 0xFF) * 4]] ^ TBox_7[TBox_2[((ctx_temp[1] >> 0x8) & 0xFF) * 4]];
ctx_temp[2] = TBox_8[TBox_2[(ctx_temp[2] & 0xFF) * 4]] ^ TBox_5[TBox_2[(ctx_temp[2] >> 0x18) * 4]] ^ TBox_6[TBox_2[((ctx_temp[2] >> 0x10) & 0xFF) * 4]] ^ TBox_7[TBox_2[((ctx_temp[2] >> 0x8) & 0xFF) * 4]];
ctx_temp[3] = TBox_8[TBox_2[(ctx_temp[3] & 0xFF) * 4]] ^ TBox_5[TBox_2[(ctx_temp[3] >> 0x18) * 4]] ^ TBox_6[TBox_2[((ctx_temp[3] >> 0x10) & 0xFF) * 4]] ^ TBox_7[TBox_2[((ctx_temp[3] >> 0x8) & 0xFF) * 4]];
}
return 1;
}
int XYAES_decrypt(const unsigned char* in, unsigned char* out, unsigned int* ctx) {
int temp[4] = {0};
int temp1[4] = {0};
temp[0] = bswap32(*(int*)&in[0]) ^ ctx[0]; // 0xda2efc91
temp[1] = bswap32(*(int*)&in[4]) ^ ctx[1]; // 0x6676ee58
temp[2] = bswap32(*(int*)&in[8]) ^ ctx[2]; // 0x4798441b
temp[3] = bswap32(*(int*)&in[12]) ^ ctx[3]; // 0x0a4cb8e6
int v8 = ctx[60] >> 1;
unsigned int nn = (temp[0] >> 0x18) & 0xFF;
while (true) {
// 0xf749e980
temp1[0] = TBox_5[(temp[0] >> 0x18) & 0xFF] ^ TBox_6[(temp[3] >> 0x10) & 0xFF] ^ TBox_7[(temp[2] >> 0x8) & 0xFF] ^ TBox_8[(temp[1] & 0xFF)] ^ ctx[4];
// 0x9402e8f9
temp1[1] = TBox_5[(temp[1] >> 0x18) & 0xFF] ^ TBox_6[(temp[0] >> 0x10) & 0xFF] ^ TBox_7[(temp[3] >> 0x8) & 0xFF] ^ TBox_8[(temp[2] & 0xFF)] ^ ctx[5];
// 0x0739f861
temp1[2] = TBox_5[(temp[2] >> 0x18) & 0xFF] ^ TBox_6[(temp[1] >> 0x10) & 0xFF] ^ TBox_7[(temp[0] >> 0x8) & 0xFF] ^ TBox_8[(temp[3] & 0xFF)] ^ ctx[6];
// 0xba9c50fc
temp1[3] = TBox_5[(temp[3] >> 0x18) & 0xFF] ^ TBox_6[(temp[2] >> 0x10) & 0xFF] ^ TBox_7[(temp[1] >> 0x8) & 0xFF] ^ TBox_8[(temp[0] & 0xFF)] ^ ctx[7];
ctx += 8;
if (! --v8) {
break;
}
// 0xd1bfde6f
temp[0] = TBox_5[(temp1[0] >> 0x18) & 0xFF] ^ TBox_6[(temp1[3] >> 0x10) & 0xFF] ^ TBox_7[(temp1[2] >> 0x8) & 0xFF] ^ TBox_8[temp1[1] & 0xFF] ^ ctx[0];
// 0x91845ad9
temp[1] = TBox_5[(temp1[1] >> 0x18) & 0xFF] ^ TBox_6[(temp1[0] >> 0x10) & 0xFF] ^ TBox_7[(temp1[3] >> 0x8) & 0xFF] ^ TBox_8[temp1[2] & 0xFF] ^ ctx[1];
// 0xbebec972
temp[2] = TBox_5[(temp1[2] >> 0x18) & 0xFF] ^ TBox_6[(temp1[1] >> 0x10) & 0xFF] ^ TBox_7[(temp1[0] >> 0x8) & 0xFF] ^ TBox_8[temp1[3] & 0xFF] ^ ctx[2];
// 0x79e64e58
temp[3] = TBox_5[(temp1[3] >> 0x18) & 0xFF] ^ TBox_6[(temp1[2] >> 0x10) & 0xFF] ^ TBox_7[(temp1[1] >> 0x8) & 0xFF] ^ TBox_8[temp1[0] & 0xFF] ^ ctx[3];
}
/* ------------------------------------------------------------------------------ */
unsigned int v3 = ((rsbox[HIBYTE((temp1[0] >> 0x10))] << 0x18) | (rsbox[BYTE2(temp1[3])] << 0x10) | (rsbox[(temp1[2] >> 0x8) & 0xFF] << 0x8) | (rsbox[temp1[1] & 0xFF])) ^ ctx[0];
out[0] = HIBYTE(v3 >> 0x10);
out[1] = BYTE2(v3);
out[2] = BYTE1(v3);
out[3] = v3;
unsigned int v4 = ((rsbox[HIBYTE((temp1[1] >> 0x10))] << 0x18) | (rsbox[BYTE2(temp1[0])] << 0x10) | (rsbox[temp1[3] >> 0x8 & 0xFf] << 0x8) | (rsbox[temp1[2] & 0xFF])) ^ ctx[1];
out[4] = HIBYTE(v4 >> 0x10);
out[5] = BYTE2(v4);
out[6] = BYTE1(v4);
out[7] = v4;
unsigned int v5 = ((rsbox[HIBYTE((temp1[2] >> 0x10))] << 0x18) | (rsbox[BYTE2(temp1[1])] << 0x10) | (rsbox[temp1[0] >> 0x8 & 0xFF] << 0x8) | (rsbox[temp1[3] & 0xFF])) ^ ctx[2];
out[8] = HIBYTE(v5 >> 0x10);
out[9] = BYTE2(v5);
out[10] = BYTE1(v5);
out[11] = v5;
unsigned int v6 = ((rsbox[HIBYTE((temp1[3] >> 0x10))] << 0x18) | (rsbox[BYTE2(temp1[2])] << 0x10) | (rsbox[temp1[1] >> 0x8 & 0xFF] << 0x8) | rsbox[temp1[0] & 0xFF]) ^ ctx[3];
out[12] = HIBYTE(v6 >> 0x10);
out[13] = BYTE2(v6);
out[14] = BYTE1(v6);
int result = v6 & 0xFF;
out[15] = v6;
return result;
}
//sub_D37CE194
void GenrateResult(int* key, const unsigned char* in, unsigned char* out, int len, unsigned int* ctx) {
// 六轮结果
// 33 01 32 34 04 02 08 61 66 7A 66 66 07 17 66 39
// 02 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
//
// 97 5C 4C D1 BD DD 18 3A 29 72 F9 16 E1 C7 8B 06
// 51 F9 44 08 66 D7 46 3C F9 67 7D 54 A1 47 0D 8B
//
// 36 51 CC 17 D3 9F 82 D2 C1 93 A4 25 04 0E 61 06
// 66 A1 D1 3B 1E CD 91 38 0C 53 AC 80 66 BC BB 8E
//
// E1 F1 B8 68 9B E7 E3 35 42 40 B3 72 15 4A 4B 66
// 9D E2 0A B6 80 19 13 70 61 AD 31 86 03 67 7F 42
//
// 08 32 12 D8 A0 29 3E 25 7A BF C4 9A D4 61 B6 EF
// BD FD 81 B7 E0 A7 49 4B 8E 0C 15 AE EE 1D D7 EA
//
// EA C2 36 CB A6 0E 7F 9F B7 7B 52 5A 2C 5A 67 75
// 10 10 10 10 10 10 10 10 10 10 10 10 10 10 10 10
// key = 0x34320131;
// v21 = 0x39661707;
// v20 = 0x66667A66;
// v19 = 0x61080204;
unsigned char res[256] = {0};
unsigned char xor_byte[] = {0x31 ,0x01 ,0x32 ,0x34 ,0x04 ,0x02 ,0x08 ,0x61 ,0x66 ,0x7A ,0x66 ,0x66 ,0x07 ,0x17 ,0x66 ,0x39};
for (int i = 0; i < len; i += 16) {
XYAES_decrypt(in + i,out + i,ctx);
for (int j = 0; j < 16; ++j) {
res[j] = (out + i)[j] ^ xor_byte[j];
xor_byte[j] = (in + i)[j];
}
printf("in :");
for (int l = 0; l < 16; ++l) {
printf("%02x ",(out)[l]);
}
printf("\r\n");
printf("out:");
for (int k = 0; k < 16; ++k) {
printf("%02x ",res[k]);
}
printf("\r\n");
}
}
void XYAES_encrypt(const unsigned char* in, unsigned char* out, unsigned int* ctx) {
}
void xyAes::testAesDec(char* in, char* out,char *aesKey) {
//70c59259-7e91-3e8 nexus5
//f7ad5eb3-5ba8-341 pixel2
// char * key = "70c59259-7e91-3e8";
unsigned int ctx[1024] = {0};
AesInitCtx(reinterpret_cast<const int *>(aesKey), 128, ctx);
GenrateResult(reinterpret_cast<int *>(aesKey), reinterpret_cast<const unsigned char *>(in),
reinterpret_cast<unsigned char *>(out), 0x60, ctx);
}
//
// Created by smallsun on 2021/4/17.
//
#include <cstring>
#include <cstdio>
#include "xyMd5.h"
typedef unsigned int uint;
template<class T> T __ROR4__(T value, uint count)
{
return (value << (0x20 - count)) | (value >> count);
}
typedef struct {
int buffer[348];
}MD5_CTX;
unsigned char k[256] = {
0x78, 0xA4, 0x6A, 0xD7, 0x56, 0xB7, 0xC7, 0xE8, 0xDB, 0x70, 0x20, 0x24, 0xEE, 0xCE, 0xBD, 0xC1,
0xAF, 0x0F, 0x7C, 0xF5, 0x2A, 0xC6, 0x87, 0x47, 0x13, 0x46, 0x30, 0xA8, 0x01, 0x95, 0x46, 0xFD,
0xD8, 0x98, 0x80, 0x69, 0xAF, 0xF7, 0x44, 0x8B, 0xB1, 0x5B, 0xFF, 0xFF, 0xBE, 0xD7, 0x5C, 0x89,
0x22, 0x11, 0x90, 0x6B, 0x93, 0x71, 0x98, 0xFD, 0x8E, 0x43, 0x79, 0xA6, 0x21, 0x08, 0xB4, 0x49,
0x62, 0x25, 0x1E, 0xF6, 0x40, 0xB3, 0x40, 0xC0, 0x51, 0x5A, 0x5E, 0x26, 0xAA, 0xC7, 0xB6, 0xE9,
0x5D, 0x10, 0x2F, 0xD6, 0x53, 0x14, 0x44, 0x02, 0x81, 0xE6, 0xA1, 0xD8, 0xC8, 0xFB, 0xD3, 0xE7,
0xE6, 0xCD, 0xE1, 0x21, 0xD6, 0x07, 0x37, 0xC3, 0x87, 0x0D, 0xD5, 0xF4, 0xED, 0x14, 0x5A, 0x45,
0x05, 0xE9, 0xE3, 0xA9, 0xF8, 0xA3, 0xEF, 0xFC, 0xD9, 0x02, 0x6F, 0x67, 0x8A, 0x4C, 0x2A, 0x8D,
0x42, 0x39, 0xFA, 0xFF, 0x81, 0xF6, 0x71, 0x87, 0x22, 0x61, 0x9D, 0x6D, 0x0C, 0x38, 0xE5, 0xFD,
0x44, 0xEA, 0xBE, 0xA4, 0xA9, 0xCF, 0xDE, 0x4B, 0x60, 0x4B, 0xBB, 0xF6, 0x70, 0xBC, 0xBF, 0xBE,
0xC6, 0x7E, 0x9B, 0x28, 0xFA, 0x27, 0xA1, 0xEA, 0x85, 0x30, 0xEF, 0xD4, 0x05, 0x1D, 0x88, 0x04,
0x39, 0xD0, 0xD4, 0xD9, 0xE5, 0x99, 0xDB, 0xE6, 0xF8, 0x7C, 0xA2, 0x1F, 0x65, 0x56, 0xAC, 0xC4,
0x44, 0x22, 0x29, 0xF4, 0x97, 0xFF, 0x2A, 0x43, 0xA7, 0x23, 0x94, 0xAB, 0x39, 0xA0, 0x93, 0xFC,
0xC3, 0x59, 0x5B, 0x65, 0x92, 0xCC, 0x0C, 0x8F, 0x7D, 0xF4, 0xEF, 0xFF, 0xD1, 0x5D, 0x84, 0x85,
0x4F, 0x7E, 0xA8, 0x6F, 0xE0, 0xE6, 0x2C, 0xFE, 0x14, 0x43, 0x01, 0xA3, 0xA1, 0x11, 0x08, 0x4E,
0x82, 0x7E, 0x53, 0xF7, 0x35, 0xF2, 0x3A, 0xBD, 0xBB, 0xD2, 0xD7, 0x2A, 0x91, 0xD3, 0x86, 0xEB
};
int MD5Init(MD5_CTX* ctx) {
ctx->buffer[0] = 0x10325476;
ctx->buffer[1] = 0x98BADCFE;
ctx->buffer[2] = 0xEFCDAB89;
ctx->buffer[3] = 0x67452301;
memcpy(&(ctx->buffer[23]), k, 256);
};
int MD5Transform(MD5_CTX* ctx,unsigned char* in,int len) {
unsigned int r0 = 0;
unsigned int var_2C = 0;
unsigned int var_30 = 0;
unsigned int var_34 = 0;
unsigned int var_38 = 0;
unsigned int var_1C = 0;
unsigned int var_24 = 0;
unsigned int var_28 = 0;
unsigned int var_3C = 0;
unsigned int var_40 = 0;
unsigned int var_44 = 0;
unsigned int var_48 = 0;
unsigned int var_20 = 0;
unsigned int var_4C = 0;
unsigned int var_50 = 0;
unsigned int var_54 = 0;
unsigned int var_58 = 0;
unsigned int var_5C = 0;
unsigned int var_60 = 0;
unsigned int var_64 = 0;
unsigned int var_68 = 0;
unsigned int var_6C = 0;
unsigned int var_204 = len;
while (true) {
int res = var_204--;
if (!res) {
break;
}
int a = ctx->buffer[0];
int b = ctx->buffer[1];
int c = ctx->buffer[2];
int d = ctx->buffer[3];
var_2C = in[0] | (in[1] << 0x8);
var_2C = var_2C | (in[2] << 0x10);
var_2C = var_2C | (in[3] << 0x18);
var_30 = var_2C;
var_2C = in[4] | (in[5] << 0x8);
var_2C = var_2C | (in[6] << 0x10);
var_2C = var_2C | (in[7] << 0x18);
var_34 = var_2C;
var_1C = __ROR4__((ctx->buffer[23] + var_30) + (((c ^ d) & b) ^ d) + a,26) + b;
var_2C = in[8] | (in[9] << 0x8);
var_2C = var_2C | (in[10] << 0x10);
var_2C = var_2C | (in[11] << 0x18);
var_38 = var_2C;
var_28 = __ROR4__((var_34 + ctx->buffer[24]) + (((b ^ c) & var_1C) ^ c) + d,19);
var_28 = var_1C + var_28;
var_2C = in[12] | (in[13] << 0x8);
var_2C = var_2C | (in[14] << 0x10);
var_2C = var_2C | (in[15] << 0x18);
var_3C = var_2C;
var_24 = __ROR4__((var_38 + ctx->buffer[25]) + (((var_1C ^ b) & var_28) ^ b) + c,15);
var_24 = var_28 + var_24;
var_2C = in[16] | (in[17] << 0x8);
var_2C = var_2C | (in[18] << 0x10);
var_2C = var_2C | (in[19] << 0x18);
var_40 = var_2C;
var_20 = __ROR4__((var_3C + ctx->buffer[26]) + (((var_28 ^ var_1C) & var_24) ^ var_1C) + b,11);
var_20 = var_24 + var_20;
var_2C = in[20] | (in[21] << 0x8);
var_2C = var_2C | (in[22] << 0x10);
var_2C = var_2C | (in[23] << 0x18);
var_44 = var_2C;
var_1C = __ROR4__((var_40 + ctx->buffer[27]) + (((var_24 ^ var_28) & var_20) ^ var_28) + var_1C,25) + var_20;
var_2C = in[24] | (in[25] << 0x8);
var_2C = var_2C | (in[26] << 0x10);
var_2C = var_2C | (in[27] << 0x18);
var_48 = var_2C;
var_28 = __ROR4__((var_44 + ctx->buffer[28]) + (((var_20 ^ var_24) & var_1C) ^ var_24) + var_28,20);
var_28 = var_1C + var_28;
var_2C = in[28] | (in[29] << 0x8);
var_2C = var_2C | (in[30] << 0x10);
var_2C = var_2C | (in[31] << 0x18);
var_4C = var_2C;
var_24 = __ROR4__((var_48 + ctx->buffer[29]) + (((var_1C ^ var_20) & var_28) ^ var_20) + var_24,15);
var_24 = var_28 + var_24;
var_2C = in[32] | (in[33] << 0x8);
var_2C = var_2C | (in[34] << 0x10);
var_2C = var_2C | (in[35] << 0x18);
var_50 = var_2C;
var_20 = __ROR4__((var_4C + ctx->buffer[30]) + (((var_28 ^ var_1C) & var_24) ^ var_1C) + var_20,12);
var_20 = var_24 + var_20;
var_2C = in[36] | (in[37] << 0x8);
var_2C = var_2C | (in[38] << 0x10);
var_2C = var_2C | (in[39] << 0x18);
var_54 = var_2C;
var_1C = __ROR4__((var_50 + ctx->buffer[31] + (((var_24 ^ var_28) & var_20) ^ var_28)) + var_1C,25);
var_1C = var_20 + var_1C;
var_2C = in[40] | (in[41] << 0x8);
var_2C = var_2C | (in[42] << 0x10);
var_2C = var_2C | (in[43] << 0x18);
var_58 = var_2C;
var_28 = __ROR4__((var_54 + ctx->buffer[32]) + (((var_20 ^ var_24) & var_1C) ^ var_24) + var_28,20);
var_28 = var_1C + var_28;
var_2C = in[44] | (in[45] << 0x8);
var_2C = var_2C | (in[46] << 0x10);
var_2C = var_2C | (in[47] << 0x18);
var_5C = var_2C;
var_24 = __ROR4__((var_58 + ctx->buffer[33]) + (((var_1C ^ var_20) & var_28) ^ var_20) + var_24,16);
var_24 = var_28 + var_24;
var_2C = in[48] | (in[49] << 0x8);
var_2C = var_2C | (in[50] << 0x10);
var_2C = var_2C | (in[51] << 0x18);
var_60 = var_2C;
var_20 = __ROR4__((var_5C + ctx->buffer[34]) + (((var_28 ^ var_1C) & var_24) ^ var_1C) + var_20,10);
var_20 = var_24 + var_20;
var_2C = in[52] | (in[53] << 0x8);
var_2C = var_2C | (in[54] << 0x10);
var_2C = var_2C | (in[55] << 0x18);
var_64 = var_2C;
var_1C = __ROR4__((var_60 + ctx->buffer[35]) + (((var_24 ^ var_28) & var_20) ^ var_28) + var_1C,25);
var_1C = var_20 + var_1C;
var_2C = in[56] | (in[57] << 0x8);
var_2C = var_2C | (in[58] << 0x10);
var_2C = var_2C | (in[59] << 0x18);
var_68 = var_2C;
var_28 = __ROR4__((var_64 + ctx->buffer[36]) + (((var_20 ^ var_24) & var_1C) ^ var_24) + var_28,19);
var_28 = var_1C + var_28;
var_2C = in[60] | (in[61] << 0x8);
var_2C = var_2C | (in[62] << 0x10);
var_2C = var_2C | (in[63] << 0x18);
var_6C = var_2C;
var_24 = __ROR4__((var_68 + ctx->buffer[37]) + (((var_1C ^ var_20) & var_28) ^ var_20) + var_24,15);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_6C + ctx->buffer[38]) + (((var_28 ^ var_1C) & var_24) ^ var_1C) + var_20,10);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_34 + (ctx->buffer[39] & 0xFF00FF00)) + (((var_20 ^ var_24) & var_28) ^ var_24) + var_1C,27);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_48 + ctx->buffer[40]) + (((var_1C ^ var_20) & var_24) ^ var_20) + var_28,23);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_5C + ctx->buffer[41]) + (((var_28 ^ var_1C) & var_20) ^ var_1C) + var_24,18);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_30 + (ctx->buffer[42] & 0xFF0011FF)) + (((var_24 ^ var_28) & var_1C) ^ var_28) + var_20,12);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_44 + ctx->buffer[43]) + (((var_20 ^ var_24) & var_28) ^ var_24) + var_1C,27);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_58 + ctx->buffer[44]) + (((var_1C ^ var_20) & var_24) ^ var_20) + var_28,23);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_6C + ctx->buffer[45]) + (((var_28 ^ var_1C) & var_20) ^ var_1C) + var_24,18);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_40 + ctx->buffer[46]) + (((var_24 ^ var_28) & var_1C) ^ var_28) + var_20,12);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_54 + ctx->buffer[47]) + (((var_20 ^ var_24) & var_28) ^ var_24) + var_1C,27);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_68 + ctx->buffer[48]) + (((var_1C ^ var_20) & var_24) ^ var_20) + var_28,23);
var_28 = var_1C + var_28;
var_24 =__ROR4__((var_3C + ctx->buffer[49]) + (((var_28 ^ var_1C) & var_20) ^ var_1C) + var_24,18);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_50 + ctx->buffer[50]) + (((var_24 ^ var_28) & var_1C) ^ var_28) + var_20,12);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_64 + ctx->buffer[51]) + (((var_20 ^ var_24) & var_28) ^ var_24) + var_1C,27);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_38 + (ctx->buffer[52] & 0xFF110011)) + (((var_1C ^ var_20) & var_24) ^ var_20) + var_28,23);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_4C + ctx->buffer[53]) + (((var_28 ^ var_1C) & var_20) ^ var_1C) + var_24,18);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_60 + ctx->buffer[54]) + (((var_24 ^ var_28) & var_1C) ^ var_28) + var_20,12);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_44 + ctx->buffer[55]) + (((var_20 ^ var_24) ^ var_28) + var_1C),28);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_50 + ctx->buffer[56]) + (((var_1C ^ var_20) ^ var_24) + var_28),21);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_5C + ctx->buffer[57]) + (((var_28 ^ var_1C) ^ var_20) + var_24),16);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_68 + ctx->buffer[58]) + (((var_24 ^ var_28) ^ var_1C) + var_20),9);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_34 + ctx->buffer[59]) + (((var_20 ^ var_24) ^ var_28) + var_1C),28);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_40 + ctx->buffer[60]) + (((var_1C ^ var_20) ^ var_24) + var_28),21);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_4C + ctx->buffer[61]) + (((var_28 ^ var_1C) ^ var_20) + var_24),16);
var_24 = var_28 + var_24;
var_1C = __ROR4__((var_64 + ctx->buffer[63]) + (((var_20 ^ var_24) ^ var_28) + var_1C),28);
var_1C = var_20 + var_1C;
var_20 = __ROR4__((var_58 + ctx->buffer[62]) + (((var_24 ^ var_28) ^ var_1C) + var_20),9);
var_20 = var_24 + var_20;
var_24 = __ROR4__((var_3C + ctx->buffer[65]) + (((var_28 ^ var_1C) ^ var_20) + var_24),16);
var_24 = var_28 + var_24;
var_28 = __ROR4__((var_30 + ctx->buffer[64]) + (((var_1C ^ var_20) ^ var_24) + var_28),21);
var_28 = var_1C + var_28;
var_20 = __ROR4__((var_48 + ctx->buffer[66]) + (((var_24 ^ var_28) ^ var_1C) + var_20),9);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_54 + ctx->buffer[67]) + (((var_20 ^ var_24) ^ var_28) + var_1C),28);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_60 + ctx->buffer[68]) + (((var_1C ^ var_20) ^ var_24) + var_28),21);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_6C + ctx->buffer[69]) + (((var_28 ^ var_1C) ^ var_20) + var_24),16);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_38 + ctx->buffer[70]) + (((var_24 ^ var_28) ^ var_1C) + var_20),9);
var_20 = var_24 + var_20;
// orn 或非操作
// bic 与非操作
var_1C = __ROR4__((var_30 + ctx->buffer[71]) + (((var_20 |~ var_28) ^ var_24) + var_1C),26);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_4C + ctx->buffer[72]) + (((var_1C |~ var_24) ^ var_20) + var_28),22);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_68 + ctx->buffer[73]) + (((var_28 |~ var_20) ^ var_1C) + var_24),17);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_44 + ctx->buffer[74]) + (((var_24 |~ var_1C) ^ var_28) + var_20),11);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_60 + ctx->buffer[75]) + (((var_20 |~ var_28) ^ var_24) + var_1C),26);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_3C + ctx->buffer[76]) + (((var_1C |~ var_24) ^ var_20) + var_28),22);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_58 + ctx->buffer[77]) + (((var_28 |~ var_20) ^ var_1C) + var_24),17);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_34 + ctx->buffer[78]) + (((var_24 |~ var_1C) ^ var_28) + var_20),11);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_50 + ctx->buffer[79]) + (((var_20 |~ var_28) ^ var_24) + var_1C),26);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_6C + ctx->buffer[80]) + (((var_1C |~ var_24) ^ var_20) + var_28),22);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_48 + ctx->buffer[81]) + (((var_28 |~ var_20) ^ var_1C) + var_24),17);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_64 + ctx->buffer[82]) + (((var_24 |~ var_1C) ^ var_28) + var_20),11);
var_20 = var_24 + var_20;
var_1C = __ROR4__((var_40 + ctx->buffer[83]) + (((var_20 |~ var_28) ^ var_24) + var_1C),26);
var_1C = var_20 + var_1C;
var_28 = __ROR4__((var_5C + ctx->buffer[84]) + (((var_1C |~ var_24) ^ var_20) + var_28),22);
var_28 = var_1C + var_28;
var_24 = __ROR4__((var_38 + ctx->buffer[85]) + (((var_28 |~ var_20) ^ var_1C) + var_24),17);
var_24 = var_28 + var_24;
var_20 = __ROR4__((var_54 + ctx->buffer[86]) + (((var_24 |~ var_1C) ^ var_28) + var_20),11);
var_20 = var_24 + var_20;
ctx->buffer[0] = ctx->buffer[0] + var_1C;
ctx->buffer[1] = ctx->buffer[1] + var_20;
ctx->buffer[2] = ctx->buffer[2] + var_24;
ctx->buffer[3] = ctx->buffer[3] + var_28;
in += 64;
for (int i = 0; i < 4; ++i) {
printf("%02x ",ctx->buffer[i]);
}
printf("\r\n");
}
for (int i = 0; i < 4; ++i) {
printf("%02x ",ctx->buffer[i]);
}
};
int MD5Update(MD5_CTX* ctx,unsigned char* in,unsigned int length) {
unsigned int count0 = 0;
unsigned int count1 = 0;
unsigned int partlen = 0;
if (length != 0) {
count0 = ctx->buffer[4] + (length << 0x3); //bits数
if (count0 < ctx->buffer[4]) {
ctx->buffer[5] += 1;
}
ctx->buffer[5] = ctx->buffer[5] + (length >> 29);
ctx->buffer[4] = count0;
partlen = ctx->buffer[22];
if (partlen == 0) {
partlen = length >> 0x6;
if (partlen == 0) {
//保存剩余长度
ctx->buffer[22] = length;
memcpy(&ctx->buffer[6],in,length);
return 1;
}
MD5Transform(ctx,in,partlen);
partlen = partlen << 0x6;
// 加上原始长度 移到in尾部
length = length - partlen;
if (length == 0) {
return 1;
}
ctx->buffer[22] = length;
memcpy(&ctx->buffer[6],in + partlen,length);
return 1;
}
// unsigned int var_20 = ctx->state[6];
// if (length > 0x3F) {
// //memcpy();
// //MD5Transform();
// }
//
// if (length > 0x40) {
// //memcpy();
// }
}
return 1;
}
void xyMd5::GenrateResult(unsigned char* url,char* out) {
unsigned char aesDecode[64] = {
0x96, 0x9A, 0x84, 0x5B, 0x29, 0xA7, 0x51, 0x56, 0x4A, 0x0D, 0x47, 0x24, 0x29, 0x02, 0x25, 0x6C,
0x9E, 0x46, 0xE2, 0xDB, 0xE2, 0x89, 0xC7, 0x64, 0x0F, 0x57, 0xE5, 0x57, 0x80, 0xC1, 0xCD, 0xD5,
0x46, 0x4E, 0x38, 0x92, 0xA6, 0xDC, 0x18, 0x69, 0x90, 0xF8, 0x85, 0xD7, 0xED, 0xDB, 0xAD, 0x0A,
0xFC, 0x2C, 0x43, 0x8F, 0x44, 0x19, 0xCD, 0xA3, 0xFA, 0xF2, 0x39, 0x82, 0xAB, 0x8F, 0x09, 0xE2
};
unsigned char xor36[64] = {0};
unsigned char xor5c[64] = {0};
unsigned int remainLen = 0;
MD5_CTX ctx;
MD5_CTX ctx1;
MD5Init(&ctx);
MD5Init(&ctx1);
for (int i = 0; i < 64; ++i) {
xor36[i] = aesDecode[i] ^ 0x36;
}
for (int i = 0; i < 64; ++i) {
xor5c[i] = aesDecode[i] ^ 0x5c;
}
MD5Update(&ctx,xor36, 64);
MD5Update(&ctx1,xor5c, 64);
// 用xor36的 ctx
// 读取请求内容
MD5Update(&ctx, url, strlen(reinterpret_cast<const char *>(url)));
remainLen = ctx.buffer[22];
// 剩余数据尾部写入0x80写入一字节
*((unsigned char*)(ctx.buffer) + 24 + remainLen) = 0x80;;
remainLen += 1;
// if (remainLen >= 0x39) {
// //MD5Transform(&ctx, reinterpret_cast<unsigned char *>(ctx.state[6]), 1);
// }
// 保存ctx.state[4]的八字节到这里
ctx.buffer[6 + 0x38 / 4] = ctx.buffer[4];
MD5Transform(&ctx, reinterpret_cast<unsigned char *>(&ctx.buffer[6]), 1);
ctx.buffer[22] = 0;
memset(&ctx.buffer[6],0,0x40);
/*开始用ctx1*/
// 用xor5c的ctx 对上一步的数据进行计算
MD5Update(&ctx1, reinterpret_cast<unsigned char *>(&ctx.buffer[0]), 16);
remainLen = ctx1.buffer[22];
ctx1.buffer[6 + remainLen / 4] = 0x80;
remainLen += 1;
// 保存ctx.state[4]的八字节到这里
ctx1.buffer[6 + 0x38 / 4] = ctx1.buffer[4];
MD5Transform(&ctx1, reinterpret_cast<unsigned char *>(&ctx1.buffer[6]), 1);
ctx1.buffer[22] = 0;
memset(&ctx1.buffer[6],0,0x40);
memcpy(out,(unsigned char*)(ctx1.buffer),16);
}
//
// Created by smallsun on 2021/4/18.
//
#include <cstdio>
#include "xyXor.h"
void InitTable(unsigned int* array,unsigned int len) {
unsigned char instr[14] = {
0x73, 0x74, 0x64, 0x3A, 0x3A, 0x61, 0x62, 0x6F, 0x72, 0x74, 0x28, 0x29, 0x3B, 0x00
};
unsigned int r0 = 0;
unsigned int var_1C = 0;
unsigned int var_24 = 0;
unsigned int var_20 = 0;
for (int i = 0; i <= 0xFF; i++) {
array[i] = i;
}
for (int i = 0; i <= 0xFF; i += 4) {
var_1C = array[i];
var_24 = (array[i] + instr[var_20] + var_24) & 0xFF;
var_20 += 1;
if (var_20 == len) {
var_20 = 0;
}
array[i] = array[var_24];
array[var_24] = var_1C;
var_1C = array[i + 1];
var_24 = (instr[var_20] + var_1C + var_24) & 0xFF;
var_20 += 1;
if (var_20 == len) {
var_20 = 0;
}
array[i + 1] = array[var_24];
array[var_24] = var_1C;
var_1C = array[i + 2];
var_24 = (instr[var_20] + var_1C + var_24) & 0xFF;
var_20 += 1;
if (var_20 == len) {
var_20 = 0;
}
array[i + 2] = array[var_24];
array[var_24] = var_1C;
var_1C = array[i + 3];
var_24 = (instr[var_20] + var_1C + var_24) & 0xFF;
var_20 += 1;
if (var_20 == len) {
var_20 = 0;
}
array[i + 3] = array[var_24];
array[var_24] = var_1C;
}
printf("Init end...\r\n");
}
void XorResult(unsigned int* table,unsigned char* in,unsigned int len,unsigned char* out) {
unsigned int var_2C = 0;
unsigned int var_30 = 0;
unsigned int var_38 = 0;
unsigned int var_34 = 0;
unsigned int var_3C = 0;
var_3C = len >> 0x3;
while (var_3C != 0) {
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_34 + var_30) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[0] = table[(var_34 + var_38) & 0xFF] ^ in[0];
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[1] = table[(var_34 + var_38) & 0xFF] ^ in[1];
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[2] = table[(var_34 + var_38) & 0xFF] ^ in[2];
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[3] = table[(var_34 + var_38) & 0xFF] ^ in[3];
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[4] = table[(var_34 + var_38) & 0xFF] ^ in[4];
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[5] = table[(var_34 + var_38) & 0xFF] ^ in[5];
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[6] = table[(var_34 + var_38) & 0xFF] ^ in[6];
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[7] = table[(var_34 + var_38) & 0xFF] ^ in[7];
//var_2C = (var_2C + 1) & 0xFF;
in += 8;
out += 8;
var_3C -= 1;
}
var_3C = len & 7;
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[0] = table[(var_34 + var_38) & 0xFF] ^ in[0];
var_3C = var_3C - 1;
if (!var_3C) {
return;
}
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[1] = table[(var_34 + var_38) & 0xFF] ^ in[1];
var_3C = var_3C - 1;
if (!var_3C) {
return;
}
var_2C = (var_2C + 1) & 0xFF;
var_34 = table[var_2C];
var_30 = (var_30 + var_34) & 0xFF;
var_38 = table[var_30];
table[var_2C] = var_38;
table[var_30] = var_34;
out[2] = table[(var_34 + var_38) & 0xFF] ^ in[2];
var_3C = var_3C - 1;
if (!var_3C) {
return;
}
printf("XorResult end...\r\n");
}
void xyXor::GenrateResult(unsigned char* in, unsigned char *out) {
unsigned int array[1024] = {0};
InitTable(array,13);
XorResult(array,in, 0x53, out);
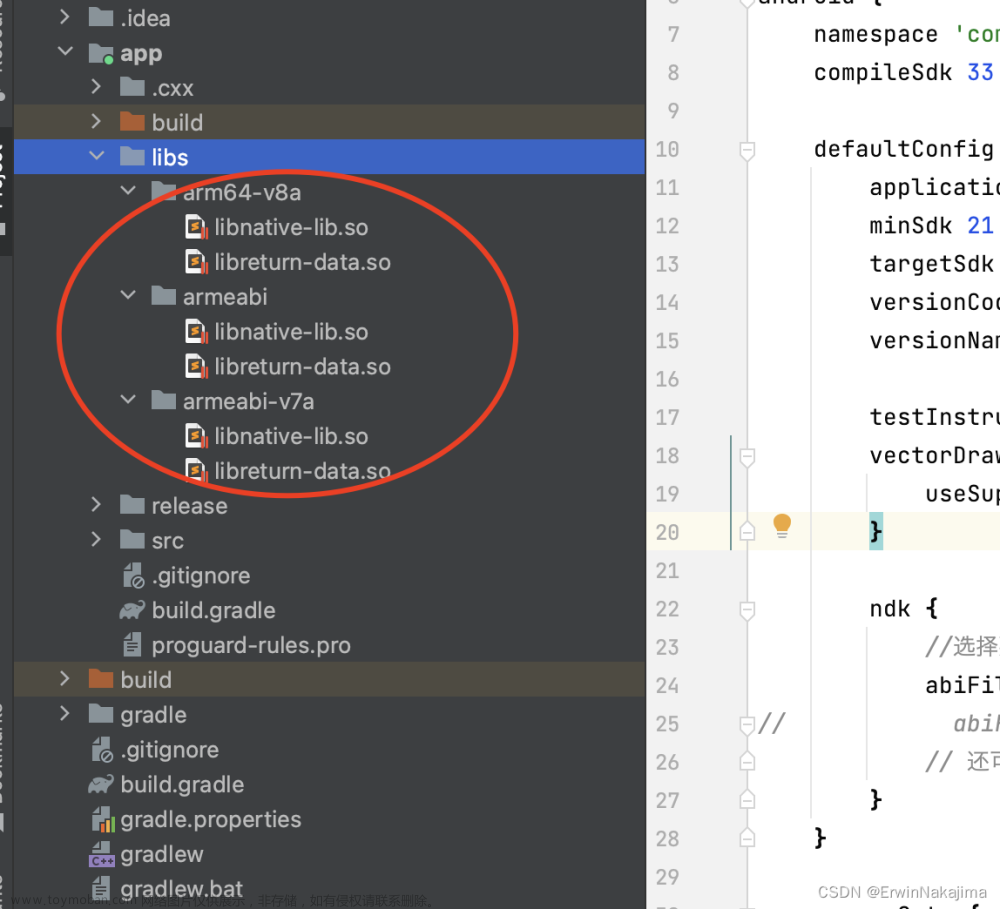
本地安装Clone 并配置cmake:


将上面代码编译成so:
g++ run.cpp -fPIC -shared -o run.so
编译后的搜放出来:传输门地址:
https://wwi.lanzoup.com/izAEa027198d文章来源:https://www.toymoban.com/news/detail-595744.html
使用python调用:文章来源地址https://www.toymoban.com/news/detail-595744.html
from ctypes import *
lib = cdll.LoadLibrary("./main.so")
lib.freeme.restype = None
lib.freeme.argtypes = [c_void_p]
lib.getXhsShield.restype = c_void_p
lib.getXhsShield.argtypes = [c_void_p, c_void_p, c_void_p]
def get_shield_cpp(shield_url_path, common_params, platform_info):
# s_xml = 'JPUl6G8k4MGEwml9FmGV1qV8UScx3IQkecsFkyLORcNmYJnHbONSjsgi2ZaSNhRGvm6FY7iYeaZpB1frFhqwlWzVgtUcByKgLNsMLFPYi7HDdhf23YR573g8ggnNwV5e'
# s_xml = 'eSwKRbpB4OfG+D8ofTHooZrXr1b0B+ZDVsxHEr7K7yTWiiVX/bZl0E8D6+6645aLIAZ0+geJrjMLyyrXA99xApWvssdRm01Cg8PRVJhEvWqyHNAS73/z0OLspXVmhaSs'
s_xml = 'a9+xPqTwWr7ua8QlDuTyLjvNTAszAxbIhBWeugeCNpcorLQJTUiH6JbLFDrW1cypknldr7izHSeoGQ1HzB6VAVu7iMG6FU1+bEt7/e+9cx6LmeDCOKSapcI9elpXr9ba'
s_xml = s_xml.encode()
shield_url = f'{shield_url_path}{common_params}{platform_info}'.encode()
# aes_key = '70c59259-7e91-3e8'.encode()
aes_key = '1d41ebdc-86dd-33e'.encode()
aes_key = '81e30ab8-2b81-33d'.encode()
ptr = lib.getXhsShield(s_xml, shield_url, aes_key)
# lib.freeme(ptr)
# print('XY' + cast(ptr, c_char_p).value.decode())
shield = 'XY' + cast(ptr, c_char_p).value.decode()
print(shield)
lib.freeme(ptr)
return shield
if __name__ == '__main__':
# common_params = 'deviceId=26a42bc5-251e-3643-9dae-6fb99195d573&identifier_flag=2&tz=Asia%2FShanghai&fid=16419676771012f8b5e741923e7c7d93279b1f4d24ee&app_id=ECFAAF01&device_fingerprint1=20180228185909b2e5364323077785b0315af9140e0d3801afbcb1c4756a33&uis=light&launch_id=1644373803&project_id=ECFAAF&device_fingerprint=20180228185909b2e5364323077785b0315af9140e0d3801afbcb1c4756a33&versionName=6.87.0&platform=android&sid=session.1644374320464773027585&t=1644374842&build=6870213&x_trace_page_current=note_detail_r10&lang=zh-Hans&channel=YingYongBao'
# platform_info = 'platform=android&build=6870213&deviceId=26a42bc5-251e-3643-9dae-6fb99195d573'
# shield_url = '/api/sns/v3/user/info?user_id=5abb06e74eacab68259b3b51'
common_params = "fid=162988201010e62257db56717f42068a3d56cc4cd8f1&device_fingerprint=20210621164233f1abe938f11f4371dad0e9cb3764ef0101e128bc882febd5&device_fingerprint1=20210621164233f1abe938f11f4371dad0e9cb3764ef0101e128bc882febd5&launch_id=1629940903&tz=Asia%2FShanghai&channel=PMgdt9803121&versionName=6.89.0.1&deviceId=2b586458-dd63-3630-b79f-29b88a036ca7&platform=android&sid=session.1629882581793303421285&identifier_flag=4&t=1629947848&project_id=ECFAAF&build=6890179&x_trace_page_current=note_detail_r10&lang=zh-Hans&app_id=ECFAAF01&uis=light"
platform_info = 'platform=android&build=6890179&deviceId=81e30ab8-2b81-33dd-8435-f9404554b4b5'
shield_url = "/api/sns/v3/user/info?user_id=5aae2cffb1da1410848cc29f"
# "/api/sns/v6/homefeed?oid=homefeed_recommend&cursor_score=&geo=eyJsYXRpdHVkZSI6MC4wMDAwMDAsImxvbmdpdHVkZSI6MC4wMDAwMDB9%0A&trace_id=7e9cea5d-3e7c-3240-bf3d-20e221557b61¬e_index=0&refresh_type=1&client_volume=0.60&preview_ad=&loaded_ad=%7B%22ads_id_list%22%3A%5B%5D%7D&personalization=1&pin_note_id=&pin_note_source=&unread_begin_note_id=60da0881000000002103ef52&unread_end_note_id=60e2abe5000000000102aced&unread_note_count=6"
# '/api/sns/v1/user/teenager/statusdeviceId=70c59259-7e91-3e8b-b8f2-35855a8565b6&identifier_flag=0&tz=Asia%2FShanghai&fid=161856398010307b510d8c42675f8f332860bd48186c&app_id=ECFAAF01&device_fingerprint1=2021040810451492d7a829c8e6b091209359dfd80365a00173354acd00c486&uis=light&launch_id=1620054097&project_id=ECFAAF&device_fingerprint=2021040810451492d7a829c8e6b091209359dfd80365a00173354acd00c486&versionName=6.87.0.1&platform=android&sid=session.1619581616447127665217&t=1620055467&build=6870213&x_trace_page_current=explore_feed&lang=zh-Hans&channel=Liteplatform=android&build=6870213&deviceId=70c59259-7e91-3e8b-b8f2-35855a8565b6'
get_shield_cpp(shield_url, common_params, platform_info)
# XYAAAAAQAAAAEAAABTAAAAUzUWEe0xG1IbD9/c+qCLOlKGmTtFa+lG43AHe+FXTKxDkYCxy+QzH53w+bQLz8MpiZx+2PFnQgwbGGeJZOmljn9ngrH0bOS+shKZANLtX/pfLGub
# XYAAAAAQAAAAEAAABTAAAAUzUWEe0xG1IbD9/c+qCLOlKGmTtFa+lG43AGe+FURa5Fxde1l7RiRZ3/qulez8N/1J9+g6pkEgxNFG2NYer82S1l1OJI251Cz9CgvYm92xt+a61H
# XYAAAAAQAAAAEAAABTAAAAUzUWEe0xG1IbD9/c+qCLOlKGmTtFa+lG43AGdeFXQ6RKxNGznuc1RJ36rehez8MpiJl+2aYxFQwYGGGIYL7x2Hlk1OGfvw85YVTtxhk/7jGHg2ER
# XYAAAAAQAAAAEAAABTAAAAUzUWEe0xG1IbD9/c+qCLOlKGmTtFa+lG43AGe+FURa5Fxde1l7RiRZ3/qulez8N/1J9+g6pkEgxNFG2NYer82S1l1OJEivt79TuztScGwzl2RXrS
# XYAAAAAQAAAAEAAABTAAAAUzUWEe0xG1IbD9/c+qCLOlKGmTtFa+lG43AGe+FURa5Fxde1l7RiRZ3/qulez8N/1J9+g6pkEgxNFG2NYer82S1l1OIl0yUxt+NgJ92Iq9FPfL0h
到了这里,关于python调用so文件的文章就介绍完了。如果您还想了解更多内容,请在右上角搜索TOY模板网以前的文章或继续浏览下面的相关文章,希望大家以后多多支持TOY模板网!