你还在为安装snort报错而烦恼么?这篇文章将解决你的问题!!!
参照了以下作者的安装教程:
(11条消息) 开源入侵检测系统—Snort安装_Thgilil的博客-CSDN博客
(11条消息) bench.h:39:10: 致命错误:rpc/rpc.h:没有那个文件或目录-CSDN博客
(11条消息) snort 检测nmap_基于Kali的Snort配置和入侵检测测试_寻找猫的博客-CSDN博客
下面便进入正题吧,以下是snort的安装第一步:
首先是先安装好以下几个包:
apt-get install flex
apt-get install bison
apt-get install libpcap-dev
apt-get isnatll libpcre3-dev
apt-get isnatll libpcre3-dev
apt-get install zlibig-dev如果报错了,就用aptitude install + 包名 这条指令(记得先Apt-get isnatll aptitude)
接着先去snort官网下载daq
右键复制链接地址,接着输入以下指令:
wget https://www.snort.org/downloads/snort/daq-2.0.7.tar.gz
tar -zxvf daq-2.0.7.tar.gz
cd daq-2.0.7
./configure
make
make install
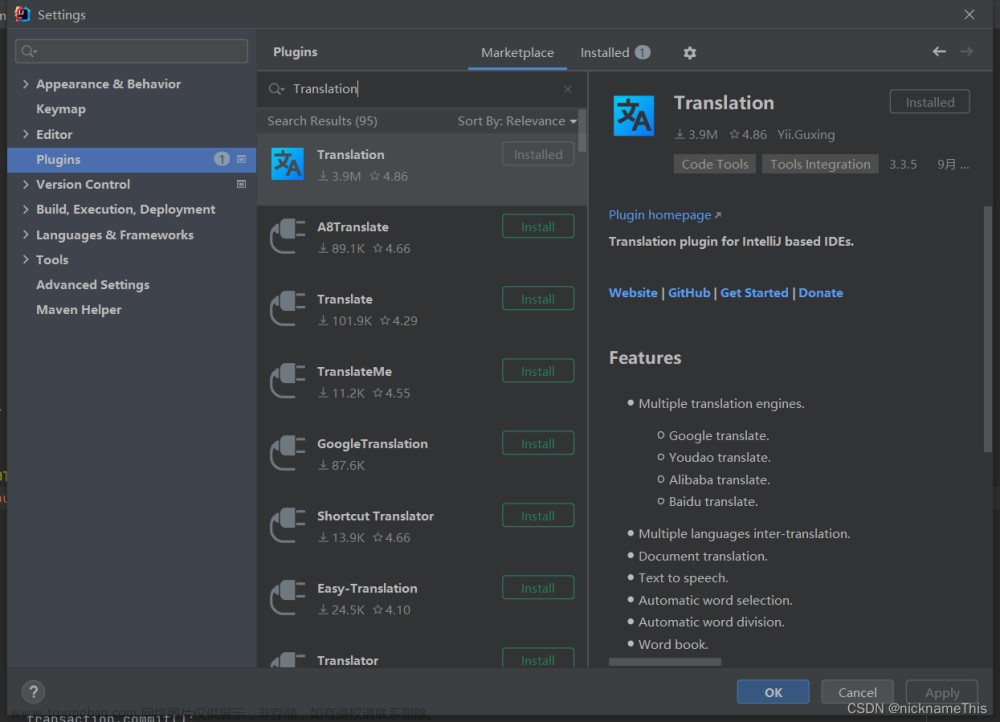
接下来在安装snort前,我们先安装LuaJIT库
wget https://luajit.org/download/LuaJIT-2.1.0-beta3.tar.gz --no-check-certificate
tar -xvzf LuaJIT-2.1.0-beta3.tar.gz
cd LuaJIT-2.1.0-beta3/src
make
cd ..
make install安装好后,我们便可以下载安装snort了,老样子,和装daq一样的,右键复制snort的链接网址,然后下载。
wget https://www.snort.org/downloads/snort/snort-2.9.20.tar.gz
tar -xvzf snort-2.9.20.tar.gz
cd snort-2.9.20.tar.gz
./configure --enable-sourcefire
make
make install会发现,报错了,这时按照提醒的安装openssl库
apt-get install openssl再用./configure --enable-sourcefire指令安装snort时,我遇到了一个很奇怪的报错:
bench.h:39:10: 致命错误:rpc/rpc.h:没有那个文件或目录
这个报错折磨了我很久,后面发现了解决方法:
将/usr/include/tirpc/rpc/*复制到/usr/include/rpc/文件夹,解决了丢失rpc.h的问题,切记rpc下的所有文件都要复制过去,并且和rpc一个文件夹的另外两个文件需要复制到include目录下。
此时我们再用./configure --enable-sourcefire指令安装snort,会发现安装成功了。(判断是否成功可以用 snort -h指令判断)
但是,当我用snort -v 时会发现全是warning。要通过安装以下服务进行配置
首先安装 web 服务组件 LAMP
Apache
sudo systemctl start nginx
sudo systemctl status nginx //检测是否在运行
sudo apt-get install apache2
sudo systemctl start apache2
sudo systemctl start firewalld //启动防火墙
sudo systemctl enable firewalld //开机自动启动
//防火墙设置开启80端口
firewall-cmd --permanent --zone=public --add-service=http
firewall-cmd --permanent --zone=public --add-service=https
firewall-cmd --reload
//查看80端口
apt-get install lsof
lsof -i:80浏览器访问IP后出现Apache页面证明成功!
接下来安装Mysql
wget http://repo.mysql.com/mysql-community-release-el7-5.noarch.rpm
rpm -ivh mysql-community-release-el7-5.noarch.rpm
//检查是否安装成功
rpm -qa | grep mysql
//启动mysql服务
systemctl start mysqld.service
systemctl enable mysqld.service
//mysql 安全设置
mysql_secure_installation然后安装PHP
apt install php
apt install php-mysql
apt install -y php-gd php-ldap php-odbc php-pear php-xml php-xmlrpc php-mbstring php-snmp php-soap
//安装php后重启apache使其生效
systemctl restart httpd.service此时我们的snort便成功下载好啦!接下来便是修改规则。
创建snort用户和组,其中snort为非特权用户
groupadd snort
useradd snort -r -s /sbin/nologin -c SNORT_IDS -g snort创建snort目录
mkdir /etc/snort
mkdir /etc/snort/rules
mkdir /etc/snort/rules/iplists
mkdir /etc/snort/preproc_rules
mkdir /usr/local/lib/snort_dynamicrules
mkdir /etc/snort/so_rules
#创建储存规则文件
touch /etc/snort/rules/iplists/black_list.rules
touch /etc/snort/rules/iplists/white_list.rules
touch /etc/snort/rules/local.rules
touch /etc/snort/sid-msg.map
#创建日志目录
mkdir /var/log/snort
mkdir /var/log/snort/archived_logs
#修改文件权限
chmod -R 5775 /etc/snort
chmod -R 5775 /var/log/snort
chmod -R 5775 /var/log/snort/archived_logs
chmod -R 5775 /etc/snort/so_rules
chmod -R 5775 /usr/local/lib/snort_dynamicrules
#修改文件属主
chown -R snort:snort /etc/snort
chown -R snort:snort /var/log/snort
chown -R snort:snort /usr/local/lib/snort_dynamicrules
#将配置文件从源文件复制到/etc/snort/中
cd /snort-2.9.18.1/etc/ # (进入snort安装目录,每个人可能不同)
cp *.conf* /etc/snort
cp *.map /etc/snort
cp *.dtd /etc/snort
cd /root/snort-2.9.18.1/src/dynamic-preprocessors/build/usr/local/lib/snort_dynamicpreprocessor
cp * /usr/local/lib/snort_dynamicpreprocessor/配置规则
wget https://www.snort.org/downloads/community/community-rules.tar.gz
tar -xvzf community-rules.tar.gz
cp community-rules/* /etc/snort/rules/
vim /etc/snort/snort.conf
//在45行附近 ipvar HOME_NET <any>修改为本机的内部网络
ipvar HOME_NET <192.168.132>.1/24 //例如
//在104行附近 配置规则文件路径
var RULE_PATH /etc/snort/rules
var SO_RULE_PATH /etc/snort/so_rules
var PREPROC_RULE_PATH /etc/snort/prepproc_rules
var WHITE_LIST_PATH /etc/snort/rules/iplists
var BLACK_LIST_PATH /etc/snort/rules/iplists
//在515行 output unified2:....... 之后添加
output unified2: filename snort.u2, limit 128
#546行,取消注释local.rules文件,后面的 include 文件均注释掉
include $RULE_PATH/local.rules
//记住,后面的全部注释掉,不然后面会报错
接着保存且退出,用以下指令检测是否成功
snort -T -c /etc/snort/snort.conf

若出现以上红框部分则证明成功了。
接下来,便是实验部分了,以下是重点!!!
vim /etc/snort/rules/local.rules //打开规则文件,写入以下规则
//检测NMAP Ping扫描
alert icmp any any -> 192.168.132.128 any (msg: "NMAP ping sweep Scan"; dsize:0;sid:10000001; rev: 1;)
//检测NMAP TCP扫描
alert tcp any any -> 192.168.132.128 any (msg: "NMAP TCP Scan";sid:10000002;rev:2;)
//检测NMAP UDP扫描
alert udp any any -> 192.168.132.128 any ( msg:"Nmap UDP Scan"; sid:10000003; rev:1; )
//检测访问 80 端口
alert tcp any any -> 192.168.132.128 80 (msg:"A test guys";reference:"A Robot";sid:1)
//检测NMAP XMAS扫描
alert tcp any any -> 192.168.132.128 any (msg:"Nmap XMAS Tree Scan"; flags:FPU; sid:1000004; rev:1; )
//检测Fing扫描
alert tcp any any -> 192.168.132.128 any (msg:"Nmap FIN Scan"; flags:F; sid:1000005; rev:1;)
保存退出后,先开一个终端用ifconfig -a指令查看自己的网络接口名称,比如我的是eth0

接着输入snort -A console -q -u snort -g snort -c /etc/snort/snort.conf -i eth0(切记这里换成你的接口名称) 激活snort控制台
以下便是对其部分操作实验返回的数据(没放全):
外界主机Ping目标靶机:

snort检测到的:

NMAP TCP 扫描

Snort反馈结果:

Nmap UDP扫描:

Snort检测结果:
 文章来源:https://www.toymoban.com/news/detail-753623.html
文章来源:https://www.toymoban.com/news/detail-753623.html
好啦,希望以上的教程可以帮助到您!文章来源地址https://www.toymoban.com/news/detail-753623.html
到了这里,关于Kali 下安装snort并且配置规则(保姆级教学)的文章就介绍完了。如果您还想了解更多内容,请在右上角搜索TOY模板网以前的文章或继续浏览下面的相关文章,希望大家以后多多支持TOY模板网!