cri-dockerd是什么?

在 Kubernetes v1.24 及更早版本中,我们使用docker作为容器引擎在k8s上使用时,依赖一个dockershim的内置k8s组件;k8s v1.24发行版中将dockershim组件给移除了;取而代之的就是cri-dockerd(当然还有其它容器接口);简单讲CRI就是容器运行时接口(Container Runtime Interface,CRI),也就是说cri-dockerd就是以docker作为容器引擎而提供的容器运行时接口;即我们想要用docker作为k8s的容器运行引擎,我们需要先部署好cri-dockerd;用cri-dockerd来与kubelet交互,然后再由cri-dockerd和docker api交互,使我们在k8s能够正常使用docker作为容器引擎;
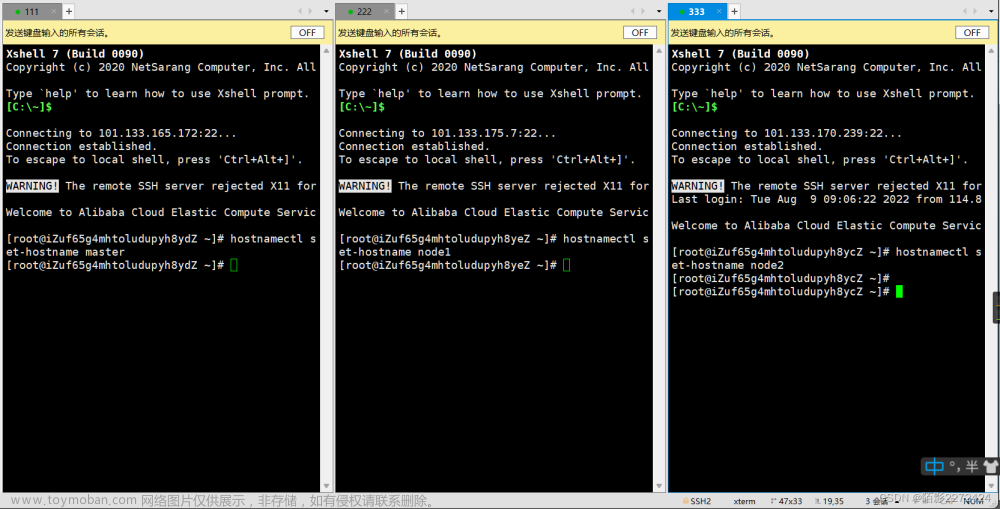
好了,接下来我们先来说一下部署环境
OS:Ubuntu 22.04.2
Container Runtime:Docker CE 23.0.1
CRI:cri-dockerd:0.3.0

以下步骤需要在每个服务器上都要部署
部署时间服务chronyd
| 1 |
|
配置阿里云时间服务器
| 1 |
|
提示:在/etc/chrony/chrony.conf中加入上述配置,将其他pool开头的配置注释掉;
重启chrony,并验证
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 |
|
提示:使用chronyc sources命令能够看到从那个服务器同步时间,能够看我们配置的服务器地址就表示chrony服务配置没有问题;
借用hosts文件做主机名解析
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 |
|
各节点禁用swap设备
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
|
提示:将fstab文件中,又不安swap设备的配置注释掉即可;
各节点禁用默认配置防火墙
| 1 2 3 4 5 |
|
安装docker
| 1 2 3 4 |
|
配置docker容器引擎使用systemd作为CGroup的驱动
| 1 2 3 4 5 6 7 8 9 10 11 |
|
提示:如果你没有代理,也可以使用registry-mirrors来指明使用的镜像加速服务;
启动docker服务
| 1 |
|
配置docker使用代理服务

| 1 2 3 |
|
提示:在/usr/lib/systemd/system/docker.service文件中加入以上配置,把自己的代理服务器地址更换上述$PROXY_SERVER_IP:$PROXY_PORT
即可;
重载和重启docker服务
| 1 2 |
|
安装cri-dockerd
| 1 2 |
|
提示:安装完cri-dockerd以后,对应服务会自动启动;
在各主机上生成kubelet和kubeadm等相关程序包的仓库
| 1 2 3 4 5 6 |
|
安装kubelet、kubeadm和kubectl
| 1 2 |
|
确认版本
| 1 2 3 |
|
整合kubelet和cri-dockerd
配置cri-dockerd

| 1 2 |
|
提示:在/usr/lib/systemd/system/cri-docker.service文件中添加上如上配置;--network-plugin:指定网络插件规范的类型,这里要使用CNI;--cni-bin-dir:指定CNI插件二进制程序文件的搜索目录;--cni-cache-dir:CNI插件使用的缓存目录;--cni-conf-dir:CNI插件加载配置文件的目录;
重启cri-dockerd服务
| 1 |
|
配置kubelet
| 1 2 3 |
|
提示:如果没有sysconfig目录,请先创建,然后再创建kubelet文件;这一步就是告诉kubelet cri-dockerd的接口在哪里;该配置不是必须的,我们也可以在初始化集群时在kubeadm命令上使用“--cri-socket unix:///run/cri-dockerd.sock”选项来告诉kubelet cri-dockerd的socket文件路径;
初始化第一个master节点
列出镜像信息
| 1 2 3 4 5 6 7 8 9 |
|
提示:k8s的镜像默认是谷歌仓库地址,需要代理才可以正常访问;如果你没有代理,请使用阿里云仓库也是可以的;用--image-repository="registry.aliyuncs.com/google_containers"来指定使用阿里云镜像仓库中的镜像部署k8s集群;
下载镜像
| 1 2 3 4 |
|
提示:这里是让我们指定cri-dockerd的socket文件路径;
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
|
提示:用上述命令就可以把初始化k8s集群所需镜像pull到本地;
初始化第一个master节点
| 1 2 3 4 5 6 7 8 |
|
提示:如果要指定仓库地址,请使用--image-repository选项来指定对应仓库;
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 |
|
提示:能够看到上诉信息,说明第一个k8s主节点就初始化成功;按照上述提示,完成后续步骤即可;
复制配置文件到本地用户家目录,并创建.kube目录
| 1 2 3 4 |
|
部署网络插件
下载网络插件calico的部署清单
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
|
在k8s集群上应用清单
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 |
|
查看节点是否准备就绪?对应calico pod是否running?
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
|
提示:能够看到master01已经准备就绪,对应pod也都正常running,到此第一个master节点就准备就绪;
加入node节点
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
|
提示:能够看到上述信息表示node节点加入成功;这里需要注意的是,加入node节点,需要指定cri-dockerd的socket文件位置;
验证:查看三个节点是否都以正常加入集群?
| 1 2 3 4 5 6 7 |
|
提示:可以看到现在有3个node节点,都处于就绪状态;
验证:kube-system名称空间下的pods是否都running?
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
|
提示:可以看到kube-system名称空间下的pod都running且都是处于就绪状态;至此基于cri-dockerd和docker的单master节点的k8s集群就搭建好了文章来源地址https://www.toymoban.com/news/detail-784956.html
到了这里,关于基于docker和cri-dockerd部署k8sv1.26.3的文章就介绍完了。如果您还想了解更多内容,请在右上角搜索TOY模板网以前的文章或继续浏览下面的相关文章,希望大家以后多多支持TOY模板网!