前言
相比较 Android8.1、9.0 而言,Android10.0 版本 的 root变得相当麻烦,10.0 中引入了动态分区机制,同样的要想完全 adb root,需要 fastboot 解锁,然后关闭 verity 才能 adb remount 成功。我尝试和之前一样修改 fstab.in.mt6765 中的 ro 和 rw 初始值,容易导致无法正常开机,在这耗费了很长时间,就暂时先跳过吧,apk root 是 ok的。
环境
| 名称 | 版本 |
|---|---|
| Android版本 | 10.0 |
| 平台 | MTK6766 |
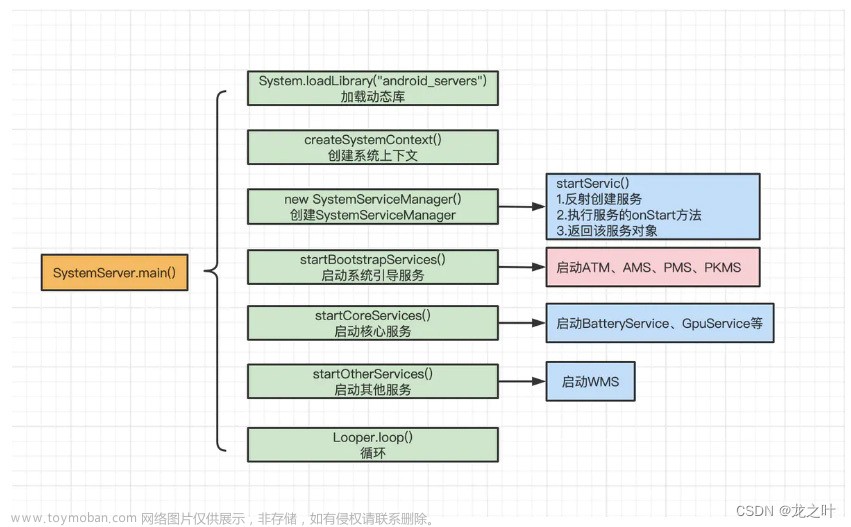
先放一张图

修改方案
上面的图就不用我多说了吧,分别用了 ROOT检测工具、RE文件管理器测试,只要 root 成功都有明显的提示,总共修改 12 个文件,新增 3 个文件,一共 15 个
modified: build/make/core/main.mk
modified: device/mediatek/sepolicy/basic/non_plat/file_contexts
modified: device/mediateksample/k62v1_64_bsp/device.mk
modified: vendor/mediatek/proprietary/bootable/bootloader/preloader/custom/k62v1_64_bsp/k62v1_64_bsp.mk
modified: system/core/adb/Android.bp
modified: system/core/adb/daemon/main.cpp
modified: system/core/init/selinux.cpp
modified: system/core/libcutils/fs_config.cpp
modified: system/core/rootdir/init.rc
modified: system/sepolicy/Android.mk
modified: system/sepolicy/prebuilts/api/29.0/public/domain.te
modified: system/sepolicy/public/domain.te
add device/mediatek/sepolicy/basic/non_plat/suproce.te
add system/extras/su/su
add system/extras/su/suproce.sh
1.让进程名称在 AS Logcat 中可见,通过修改 ro.adb.secure 和 ro.secure
ps:这步不是必须的,目的只是在 logcat 中可见进程 pid 和包名,而且打开 USB 调试时默认授权,不再弹授权框
build/make/core/main.mk
tags_to_install :=
ifneq (,$(user_variant))
# Target is secure in user builds.
- ADDITIONAL_DEFAULT_PROPERTIES += ro.secure=1
+ # ADDITIONAL_DEFAULT_PROPERTIES += ro.secure=1
+ ADDITIONAL_DEFAULT_PROPERTIES += ro.secure=0
ADDITIONAL_DEFAULT_PROPERTIES += security.perf_harden=1
ifeq ($(user_variant),user)
- ADDITIONAL_DEFAULT_PROPERTIES += ro.adb.secure=1
+ # ADDITIONAL_DEFAULT_PROPERTIES += ro.adb.secure=1
+ ADDITIONAL_DEFAULT_PROPERTIES += ro.adb.secure=0
endif
ifeq ($(user_variant),userdebug)
@@ -251,7 +253,7 @@ ifneq (,$(user_variant))
tags_to_install += debug
else
# Disable debugging in plain user builds.
- enable_target_debugging :=
+ # enable_target_debugging :=
endif
# Disallow mock locations by default for user builds
2.修改 SELinux权限为 Permissive
SELinux 常用状态有两个 Permissive 和 Enforcing,通过 adb shell getenforce 可查看当前所处模式
10.0 改到了 selinux.cpp 中
system/core/init/selinux.cpp
bool IsEnforcing() {
+ return false;
if (ALLOW_PERMISSIVE_SELINUX) {
return StatusFromCmdline() == SELINUX_ENFORCING;
}
3.关闭 DM-verity
vendor/mediatek/proprietary/bootable/bootloader/preloader/custom/k62v1_64_bsp/k62v1_64_bsp.mk
TARGET=k62v1_64_bsp
MTK_PLATFORM=MT6765
MTK_SEC_CHIP_SUPPORT=yes
-MTK_SEC_USBDL=ATTR_SUSBDL_ONLY_ENABLE_ON_SCHIP
-MTK_SEC_BOOT=ATTR_SBOOT_ENABLE
+MTK_SEC_USBDL=ATTR_SUSBDL_DISABLE
+MTK_SEC_BOOT=ATTR_SBOOT_DISABLE
MTK_SEC_MODEM_AUTH=no
MTK_SEC_SECRO_AC_SUPPORT=yes
# Platform
4.增加 su 相关,确保 apk root 权限
apk 获取 root 权限,需要内置 su 文件,参考之前 8.1 的做法,在 init.rc 中 boot_completed 时执行脚本
开机执行脚本的命令可直接加在 system/core/rootdir/init.rc
开机脚本执行是否成功,可通过 adb shell dmesg > dmesg.txt 抓取 init 的日志,搜索是否报错,或者缺少权限。
boot_completed 启动完成时,start suproce
system/core/rootdir/init.rc
class_reset main
+service suproce /system/bin/suproce.sh
+ class main
+ user root
+ group root
+ oneshot
+ seclabel u:object_r:suproce_exec:s0
+
+
on property:sys.boot_completed=1
+ start suproce
bootchart stop
system/extras/su/suproce.sh
#!/system/bin/sh
mount -o rw,remount /system
chmod 06755 su
su --daemon
echo "su daemon done."
device/mediatek/sepolicy/basic/non_plat/file_contexts
#hidl process merging
/(system\/vendor|vendor)/bin/hw/merged_hal_service u:object_r:merged_hal_service_exec:s0
+
+#suproce
+/system/bin/suproce.sh u:object_r:suproce_exec:s0
此处写法有变动,suproce.te 中要加 system_file_type,不然编译时报错
out/target/product/k62v1_64_bsp/obj/ETC/sepolicy_tests_intermediates/sepolicy_tests )"
The following types on /system/ must be associated with the "system_file_type" attribute: suproce_exec
checkpolicy: error(s) encountered while parsing configuration
device/mediatek/sepolicy/basic/non_plat/suproce.te
type suproce, coredomain;
#type suproce_exec, exec_type, vendor_file_type, file_type;
type suproce_exec, exec_type, file_type, system_file_type;
# permissive suproce;
# allow shell suproce_exec:file { read open getattr execute };
init_daemon_domain(suproce);
改完后继续编译,再次出现新错误,user 版本不允许 permissive domains
[ 19% 1135/5824] build out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy
FAILED: out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy
/bin/bash -c "(ASAN_OPTIONS=detect_leaks=0 out/host/linux-x86/bin/checkpolicy -M -c 30 -o out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy.tmp out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy.recovery.conf ) && (out/host/linux-x86/bin/sepolicy-analyze out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy.tmp permissive > out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy.permissivedomains ) && (if [ \"user\" = \"user\" -a -s out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy.permissivedomains ]; then echo \"==========\" 1>&2; echo \"ERROR: permissive domains not allowed in user builds\" 1>&2; echo \"List of invalid domains:\" 1>&2; cat out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy.permissivedomains 1>&2; exit 1; fi ) && (mv out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy.tmp out/target/product/k62v1_64_bsp/obj/ETC/sepolicy.recovery_intermediates/sepolicy )"
device/mediatek/sepolicy/bsp/plat_private/untrusted_app_all.te:7:WARNING 'unrecognized character' at token '' on line 53889:
# Purpose: Make app can get phoneEx
注释下面文件中的 exit 1
system/sepolicy/Android.mk
@@ -518,7 +518,7 @@ $(LOCAL_BUILT_MODULE): $(HOST_OUT_EXECUTABLES)/secilc $(HOST_OUT_EXECUTABLES)/se
echo "ERROR: permissive domains not allowed in user builds" 1>&2; \
echo "List of invalid domains:" 1>&2; \
cat $@.permissivedomains 1>&2; \
- exit 1; \
+ # exit 1; \
fi
$(hide) mv $@.tmp $@
@@ -562,7 +562,7 @@ $(LOCAL_BUILT_MODULE): $(sepolicy.recovery.conf) $(HOST_OUT_EXECUTABLES)/checkpo
echo "ERROR: permissive domains not allowed in user builds" 1>&2; \
echo "List of invalid domains:" 1>&2; \
cat $@.permissivedomains 1>&2; \
- exit 1; \
+ # exit 1; \
fi
$(hide) mv $@.tmp $@
再重新编译,又报错,卧底马,什么情况, 在 system/sepolicy/public/domain.te 中 335 行进行了权限检查
libsepol.report_assertion_extended_permissions: neverallowxperm on line 335 of system/sepolicy/public/domain.te (or line 11735 of policy.conf) violated by allow aee_aed suproce_exec:file { ioctl };
libsepol.report_assertion_extended_permissions: neverallowxperm on line 335 of system/sepolicy/public/domain.te (or line 11735 of policy.conf) violated by allow crash_dump suproce_exec:file { ioctl };
libsepol.check_assertions: 2 neverallow failures occurred
Error while expanding policy
libsepol.report_assertion_extended_permissions: neverallowxperm on line 335 of system/sepolicy/public/domain.te (or line 11642 of policy.conf) violated by allow aee_aed suproce_exec:file { ioctl };
libsepol.report_assertion_extended_permissions: neverallowxperm on line 335 of system/sepolicy/public/domain.te (or line 11642 of policy.conf) violated by allow crash_dump suproce_exec:file { ioctl };
libsepol.check_assertions: 2 neverallow failures occurred
Error while expanding policy
system/sepolicy/public/domain.te
system/sepolicy/prebuilts/api/29.0/public/domain.te
# All ioctls on file-like objects (except chr_file and blk_file) and
# sockets must be restricted to a whitelist.
# neverallowxperm * *:{ dir notdevfile_class_set socket_class_set blk_file } ioctl { 0 };
直接将 neverallowxperm * *:{ dir notdevfile_class_set socket_class_set blk_file } ioctl { 0 }; 这行注释就行,不过需要两个文件都注释,
开始按照忽略原则将 aee_aed、crash_dump 通过 - 的方式修改,又报其它错误(宝宝心里苦啊)
*neverallowxperm { * -aee_aed -crash_dump } :{ dir notdevfile_class_set socket_class_set blk_file } ioctl { 0 }; 这样行不通
拷贝 su 文件和开机脚本 suproce.sh 到 system/bin 目录下
device/mediateksample/k62v1_64_bsp/device.mk
@@ -19,6 +19,11 @@ PRODUCT_COPY_FILES += $(LOCAL_PATH)/sbk-kpd.kl:system/usr/keylayout/sbk-kpd.kl:m
$(LOCAL_PATH)/sbk-kpd.kcm:system/usr/keychars/sbk-kpd.kcm:mtk
endif
+PRODUCT_COPY_FILES += \
+ system/extras/su/su:system/bin/su \
+ system/extras/su/suproce.sh:system/bin/suproce.sh
给 su 文件增加权限
system/core/libcutils/fs_config.cpp
@@ -166,7 +168,9 @@ static const struct fs_path_config android_files[] = {
// the following two files are INTENTIONALLY set-uid, but they
// are NOT included on user builds.
{ 06755, AID_ROOT, AID_ROOT, 0, "system/xbin/procmem" },
- { 04750, AID_ROOT, AID_SHELL, 0, "system/xbin/su" },
+ { 06755, AID_ROOT, AID_SHELL, 0, "system/bin/su" },
// the following files have enhanced capabilities and ARE included
// in user builds.
5.解锁 fastboot,并关闭 verity 按需操作
system/core/adb/Android.bp
@@ -76,7 +76,15 @@ cc_defaults {
name: "adbd_defaults",
defaults: ["adb_defaults"],
- cflags: ["-UADB_HOST", "-DADB_HOST=0"],
+ //cflags: ["-UADB_HOST", "-DADB_HOST=0"],
+ cflags: [
+ "-UADB_HOST",
+ "-DADB_HOST=0",
+ "-UALLOW_ADBD_ROOT",
+ "-DALLOW_ADBD_ROOT=1",
+ "-DALLOW_ADBD_DISABLE_VERITY",
+ "-DALLOW_ADBD_NO_AUTH",
+ ],
product_variables: {
debuggable: {
cflags: [
system/core/adb/daemon/main.cpp
@@ -63,12 +63,13 @@ static inline bool is_device_unlocked() {
}
static bool should_drop_capabilities_bounding_set() {
- if (ALLOW_ADBD_ROOT || is_device_unlocked()) {
+ /*if (ALLOW_ADBD_ROOT || is_device_unlocked()) {
if (__android_log_is_debuggable()) {
return false;
}
}
- return true;
+ return true;*/
+ return false;
}
static bool should_drop_privileges() {
解锁时可能音量上键不生效,那需要进行对调
vendor/mediatek/proprietary/bootable/bootloader/lk/app/mt_boot/sec_unlock.c
unlock_warranty();
while (1) {
- if (mtk_detect_key(MT65XX_MENU_SELECT_KEY)) { //VOL_UP
+ //if (mtk_detect_key(MT65XX_MENU_SELECT_KEY)) { //VOL_UP
+ if (mtk_detect_key(MT65XX_MENU_OK_KEY)) { //VOL_DOWN
fastboot_info("Start unlock flow\n");
//Invoke security check after confirming "yes" by user
ret = fastboot_get_unlock_perm(&unlock_allowed);
@@ -374,7 +375,8 @@ void fastboot_oem_unlock(const char *arg, void *data, unsigned sz)
fastboot_okay("");
}
break;
- } else if (mtk_detect_key(MT65XX_MENU_OK_KEY)) { //VOL_DOWN
+ //} else if (mtk_detect_key(MT65XX_MENU_OK_KEY)) { //VOL_DOWN
+ } else if (mtk_detect_key(MT65XX_MENU_SELECT_KEY)) { //VOL_UP
video_printf("return to fastboot in 3s\n");
mdelay(3000);
fastboot_boot_menu();
去除 oem 解锁后每次开机提示 Your device has been unlocked and can’t be trusted 警告字眼
vendor/mediatek/proprietary/bootable/bootloader/lk/platform/common/boot/vboot_state.c
@@ -133,9 +133,10 @@ int orange_state_warning(void)
video_clean_screen();
video_set_cursor(video_get_rows() / 2, 0);
- video_printf(title_msg);
- video_printf("Your device has been unlocked and can't be trusted\n");
- video_printf("Your device will boot in 5 seconds\n");
+ //20191206 annotaion
+ // video_printf(title_msg);
+ // video_printf("Your device has been unlocked and can't be trusted\n");
+ // video_printf("Your device will boot in 5 seconds\n");
mtk_wdt_restart();
mdelay(5000);
mtk_wdt_restart();
获取 adb root 权限, user 版本目前还不能 remount 成功, userdebug 版本可成功 remount,
后续 user 版本 adb 成功后会持续更新,以下是操作比对
=user==========
C:>adb root
C:>adb remount
/system/bin/remount exited with status 2
remount failed
C:>adb disable-verity
Device is locked. Please unlock the device first
C:>adb reboot bootloader
C:>fastboot flashing unlock
…
(bootloader) Start unlock flow
OKAY [ 12.394s]
finished. total time: 12.398s
C:>fastboot reboot
rebooting…
finished. total time: 0.003s
C:>adb root
C:>adb disable-verity
Successfully disabled verity
Now reboot your device for settings to take effect
C:>adb reboot
C:>adb root
C:>adb remount
/system/bin/remount exited with status 2
remount failed
=userdebug==========
C:>adb root
C:>adb remount
E Skipping /system
E Skipping /vendor
E Skipping /product
W No partitions to remount
/system/bin/remount exited with status 7
remount failed
C:>adb disable-verity
Device is locked. Please unlock the device first
C:>adb reboot bootloader
C:>fastboot flashing unlock
…
(bootloader) Start unlock flow
OKAY [ 12.394s]
finished. total time: 12.398s
C:>fastboot reboot
rebooting…
finished. total time: 0.003s
C:>adb root
C:>adb disable-verity
Successfully disabled verity
Now reboot your device for settings to take effect
C:>adb reboot
C:>adb root
C:>adb remount
remount succeeded
user 版本已成功获取 adb root
6.修改 adb root 权限,编译 userdebug 版本进行比对
user 和 userdebug 区别在于 remount 时感觉走的地方不太一样,userdebug remount 时打印的日志来自 system\core\fs_mgr\fs_mgr_remount.cpp
思路为只要让 user 版本下 remount 时打印一样的日志即可
修改文件清单
modified: system/core/adb/Android.bp
modified: system/core/fs_mgr/Android.bp
modified: system/sepolicy/Android.mk
modified: system/sepolicy/definitions.mk
modified: frameworks/base/services/usb/java/com/android/server/usb/UsbDeviceManager.java
system/core/adb/Android.bp
+++ b/alps/system/core/adb/Android.bp
@@ -412,6 +412,8 @@ cc_library {
"liblog",
],
+ required: [ "remount",],
+
product_variables: {
debuggable: {
required: [
system/core/fs_mgr/Android.bp
+++ b/alps/system/core/fs_mgr/Android.bp
@@ -76,7 +76,8 @@ cc_library {
"libfstab",
],
cppflags: [
- "-DALLOW_ADBD_DISABLE_VERITY=0",
+ "-UALLOW_ADBD_DISABLE_VERITY",
+ "-DALLOW_ADBD_DISABLE_VERITY=1",
],
product_variables: {
debuggable: {
@@ -133,7 +134,8 @@ cc_binary {
"fs_mgr_remount.cpp",
],
cppflags: [
- "-DALLOW_ADBD_DISABLE_VERITY=0",
+ "-UALLOW_ADBD_DISABLE_VERITY",
+ "-DALLOW_ADBD_DISABLE_VERITY=1",
],
product_variables: {
debuggable: {
user 版本启用 overlayfs 来装载 remount 对应分区
system/sepolicy/Android.mk
+++ b/alps/system/sepolicy/Android.mk
@@ -309,7 +309,7 @@ LOCAL_REQUIRED_MODULES += \
endif
-ifneq ($(TARGET_BUILD_VARIANT), user)
+ifneq ($(TARGET_BUILD_VARIANT), eng)
LOCAL_REQUIRED_MODULES += \
selinux_denial_metadata \
@@ -1104,7 +1104,8 @@ endif
ifneq ($(filter address,$(SANITIZE_TARGET)),)
local_fc_files += $(wildcard $(addsuffix /file_contexts_asan, $(PLAT_PRIVATE_POLICY)))
endif
-ifneq (,$(filter userdebug eng,$(TARGET_BUILD_VARIANT)))
+ifneq (,$(filter user userdebug eng,$(TARGET_BUILD_VARIANT)))
local_fc_files += $(wildcard $(addsuffix /file_contexts_overlayfs, $(PLAT_PRIVATE_POLICY)))
endif
ifeq ($(TARGET_FLATTEN_APEX),true)
@@ -1166,7 +1167,9 @@ file_contexts.device.tmp :=
file_contexts.local.tmp :=
##################################
-ifneq ($(TARGET_BUILD_VARIANT), user)
+# ifneq ($(TARGET_BUILD_VARIANT), user)
+ifneq ($(TARGET_BUILD_VARIANT), eng)
include $(CLEAR_VARS)
LOCAL_MODULE := selinux_denial_metadata
system/sepolicy/definitions.mk
+++ b/alps/system/sepolicy/definitions.mk
@@ -1,10 +1,11 @@
# Command to turn collection of policy files into a policy.conf file to be
# processed by checkpolicy
define transform-policy-to-conf
@mkdir -p $(dir $@)
$(hide) m4 --fatal-warnings $(PRIVATE_ADDITIONAL_M4DEFS) \
-D mls_num_sens=$(PRIVATE_MLS_SENS) -D mls_num_cats=$(PRIVATE_MLS_CATS) \
- -D target_build_variant=$(PRIVATE_TARGET_BUILD_VARIANT) \
+ -D target_build_variant=eng \
-D target_with_dexpreopt=$(WITH_DEXPREOPT) \
-D target_arch=$(PRIVATE_TGT_ARCH) \
默认开启 OEM 解锁选项文章来源:https://www.toymoban.com/news/detail-823732.html
frameworks/base/services/usb/java/com/android/server/usb/UsbDeviceManager.java文章来源地址https://www.toymoban.com/news/detail-823732.html
+++ b/alps/frameworks/base/services/usb/java/com/android/server/usb/UsbDeviceManager.java
@@ -995,6 +995,10 @@ public class UsbDeviceManager implements ActivityTaskManagerInternal.ScreenObser
}
protected void finishBoot() {
+ android.service.oemlock.OemLockManager mOemLockManager
+ = (android.service.oemlock.OemLockManager) mContext.getSystemService(Context.OEM_LOCK_SERVICE);
+ mOemLockManager.setOemUnlockAllowedByUser(true);
+
if (mBootCompleted && mCurrentUsbFunctionsReceived && mSystemReady) {
if (mPendingBootBroadcast) {
updateUsbStateBroadcastIfNeeded(getAppliedFunctions(mCurrentFunctions));
C:>adb root
C:>adb remount
W DM_DEV_STATUS failed for scratch: No such device or address
E [liblp]No device named scratch
[liblp]Partition scratch will resize from 0 bytes to 1315950592 bytes
[liblp]Updated logical partition table at slot 0 on device /dev/block/by-name/super
[libfs_mgr]Created logical partition scratch on device /dev/block/dm-3
[libfs_mgr]superblock s_max_mnt_count:65535,/dev/block/dm-3
[libfs_mgr]__mount(source=/dev/block/dm-3,target=/mnt/scratch,type=ext4)=0: Success
Using overlayfs for /system
Using overlayfs for /vendor
Using overlayfs for /product
[libfs_mgr]__mount(source=overlay,target=/system,type=overlay,upperdir=/mnt/scratch/overlay/system/upper)=0
[libfs_mgr]__mount(source=overlay,target=/vendor,type=overlay,upperdir=/mnt/scratch/overlay/vendor/upper)=0
[libfs_mgr]__mount(source=overlay,target=/product,type=overlay,upperdir=/mnt/scratch/overlay/product/upper)=0
remount succeeded
到了这里,关于android10.0(Q) MTK 6765 user版本打开root权限的文章就介绍完了。如果您还想了解更多内容,请在右上角搜索TOY模板网以前的文章或继续浏览下面的相关文章,希望大家以后多多支持TOY模板网!