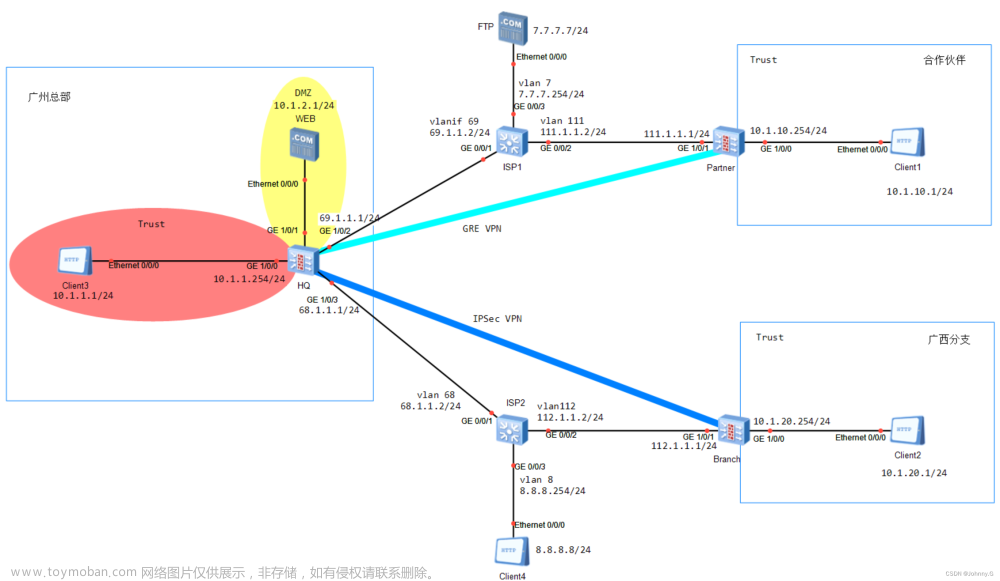
网络拓扑如上图所示,为方便记忆从左到右顺时针方向的网段的分别为192.168.1.0, 2.0, 3.0。
配置目标:两台思科防火墙之间建立IPsec VPN(野蛮模式),使得左边192.168.1.0网段能够访问右边192.168.3.0网段。左边ASA1作为连接发起端,右边ASA2作为连接接收端。在这里两边都是固定IP地址,在真实环境中发起端一般为非固定IP地址,如拨号上网的网络,光猫通过拨号动态获取IP地址,ASA1防火墙可以放在光猫的LAN口一端。接收一端必须有固定IP地址。
基本信息:该环境使用GNS3模拟软件,防火墙软件版本为9.9(2)。配置完成后ipsec连接不会自动触发,需要数据请求通过隧道才会触发,而且只能在发起端(ASA1端)触发,比如在192.168.1.2上ping 192.168.3.2,就会触发ipsec连接。
ASA1(发起连接端)防火墙配置:
基本配置:
配置主机名:
hostname ASA1
配置接口和IP地址:
int e0/0
nameif inside
ip address 192.168.1.1 255.255.255.0
no shut
int e0/1
nameif outside
ip address 192.168.2.1 255.255.255.0
no shut
配置从192.168.1.0到192.168.3.0的数据包不做地址转换,该网络拓扑比较简单,可以不配置,但是真实环境比较复杂,一般都需要配置,故这里也配置上。由于这篇文章主要讲ipsec的配置,故这里不做地址转换命令的介绍。
object network ASA1-inside
subnet 192.168.1.0 255.255.255.0
object network ASA2-inside
subnet 192.168.3.0 255.255.255.0
nat (inside,outside) source static ASA1-inside ASA1-inside destination static ASA2-inside ASA2-inside
下面配置控制连接的参数,配置后,收到连接或发出连接请求时会根据策略号由低到高的匹配对端的策略
设置1号策略,策略号可以随便填,敲入后进入二层命令行
crypto ikev1 policy 1
设置预共享密码(不是密钥),密码需要与对端一致,具体密码在通道命令里设置
authentication pre-share
设置控制连接加密方法为3des,需要与对端一致
encryption 3des
设置控制连接数据包完整性校验方法为sha,需要与对端一致
hash sha
设置密钥生成的长度,需要与对端一致,一般号码越高,越长
group 2
设置密钥更新周期,建议与对端一致
lifetime 28800
下面配置数据连接的参数:
使用隧道(esp)方式,建议使用esp. 加密方式为3des,数据完整性校验方式为sha
crypto ipsec ikev1 transform-set trans1 esp-3des esp-sha-hmac
配置NAT-T特性,这个特性使得防火墙outside接口的IP地址,如果在网络中有被转换为其他地址,则双方也能通讯,建议配置。如果outside接口的IP地址被网络中的设备NAT后没有配置这个选项,则IPSEC不能建立。这个命令后面会加一个数字表示多少秒,该数字表示周期性发送类似于心跳包的数据包,保持网络中网络设备的NAT会话不会被删除。
crypto isakmp nat-traversal 30
配置对端设备的身份识别方式(可以理解为账号名,一般登陆一个系统需要账户名和密码,密码就是预共享密码在后面配置)
简要介绍一下这个命令:
crypto isakmp identity {address | hostname | key-id 字符串 | auto}
可以看出有3种类型的识别方式, address,hostname, key-id。auto是address和hostname的综合,这里不介绍。识别方式要和对端一致。hostname的识别方式叫FQDN识别方式,hostname只是思科命令不是IPsec的术语。如果选择hostname则用户名(身份识别字符串)为设备的hostname,可以用show hostname命令查看具体字符串。ASA1建立控制连接时发送的数据包会含很多信息,其中两个信息就是:一.字符串ASA2 二.FQDN方式。
对端ASA2配置好之后,在建立控制连接的过程中也会把自身的身份发送到ASA1,其中两个信息就是:一.字符串ASA2 二. FQDN方式
在本场景中,使用识别方式为hostname方式,则FQDN身份识别方式的识别字符串为ASA1。查看之前基本配置里的配置命令(hostname ASA1)。
crypto isakmp identity hostname
配置IPSEC通道
野蛮方式的通道名为对端的身份识别字符串,对端的识别方式为FQDN方式,识别字符串为ASA2。
tunnel-group ASA2 type ipsec-l2l
配置这条命令后设备会有提示,表示该配置为数字证书或者对端为野蛮模式才会这样配,如下图所示,可以忽略这个提示。

配置预共享密码和断线检测
tunnel-group ASA2 ipsec-attributes
进入第二层命令模式
配置连接密码为123456,需与对端一致
ikev1 pre-shared-key 123456
配置IPSEC密码和断线检测,配置20秒超时后重传,重传3次判断为断线
isakmp keepalive threshold 20 retry 3
配置哪些数据包需要转发到IPSEC通道,该配置需要设置一个ACL,然后后面配置绑定这个ACL
access-list goIntoTunnel extended permit ip 192.168.1.0 255.255.255.0 192.168.3.0 255.255.255.0
注意上面这个ACL的网段必须与对端相对应,不然连接建立不起来。
比如上面这个ACL可以总结为:(本端192.168.1.0/24, 对端192.168.3.0/24)。则对端需要配置为:(本端192.168.3.0/24,对端192.168.1.0/24)。如果对端配置为:(本端192.168.3.0/27, 对端192.168.1.0/24)则不能匹配,不能建立连接。
配置cryto map。 cryto map是一个列表,该列表记录哪些数据包需要建立IPsec, 将前面配置的一些分散的信息绑定到一起形成一个ipsec连接的完整信息,这个列表有序号,序号可以随意填,匹配IPSEC参数的时候按照序号从低到高的顺序进行匹配。
设置10号入口,匹配ACL名为goIntoTunnel(该ACL已在之前设置好),需要与对端为192.168.2.1的地址建立IPSEC连接,数据连接参数为trans1(该参数已在之前设置),发起控制连接时使用野蛮模式发起连接。
crypto map mymap 10 match address goIntoTunnel
crypto map mymap 10 set peer 192.168.2.2
crypto map mymap 10 set ikev1 phase1-mode aggressive
crypto map mymap 10 set ikev1 transform-set trans1
将crypto map 绑定到outside并设置ISAKMP(Internet Security Association and Key Management Protocol)为enable。ISAKMP就是建立IPsec连接时需要使用的框架,包含一系列的规则。
crypto map mymap interface outside
crypto ikev1 enable outside
设置允许IPSEC的数据包进入防火墙
sysopt connection permit-vpn
设置192.168.3.0的数据包通过outside接口进行发送
route outside 192.168.3.0 255.255.255.0 192.168.2.2
ASA1配置完毕。
配置ASA2:
基本配置:
配置主机名:
hostname ASA2
配置接口和IP地址:
int e0/0
nameif inside
ip address 192.168.3.1 255.255.255.0
no shut
int e0/1
nameif outside
ip address 192.168.2.2 255.255.255.0
no shut
配置从192.168.3.0到192.168.1.0的数据包不做地址转换,上面已介绍过。
object network ASA1-inside
subnet 192.168.1.0 255.255.255.0
object network ASA2-inside
subnet 192.168.3.0 255.255.255.0
nat (inside,outside) source static ASA2-inside ASA2-inside destination static ASA1-inside ASA1-inside
下面配置控制连接的参数,上面已介绍过。
crypto ikev1 policy 1
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 28800
下面配置数据连接的参数,上面已介绍过:
crypto ipsec ikev1 transform-set trans1 esp-3des esp-sha-hmac
配置NAT-T特性,上面已介绍过。
crypto isakmp nat-traversal 30
配置对端设备的身份识别方式,上面已介绍过:
crypto isakmp identity hostname
配置IPSEC通道,上面已介绍过,和上面不同的是这里设置通道名为ASA1。
tunnel-group ASA1 type ipsec-l2l
配置预共享密码和断线检测,上面已介绍过:
tunnel-group ASA1 ipsec-attributes
ikev1 pre-shared-key 123456
isakmp keepalive threshold 20 retry 3
配置哪些数据包需要转发到IPSEC通道,上面已介绍过。
access-list goIntoTunnel extended permit ip 192.168.3.0 255.255.255.0 192.168.1.0 255.255.255.0
配置动态crypto maps:
由于野蛮模式的控制连接只需要设备认证方式和预共享密码匹配就能连接,对于接收端来说发起端的IP地址不知道(相当于信息不全),需要设置到动态crypto maps(Dynamic Crypto Maps)里。静态crypto maps就是ASA1里面配置的crypto maps那样。动态crypto maps只设置在野蛮模式的接收端,和静态crypto maps一样,也是把一些分散的信息集中起来形成一个完整的ipsec连接信息,里面的匹配规则也和静态crypto maps一样从低到高匹配,配置方式也和静态crypto maps一样。设置好之后,最终也要绑定到静态crypto maps上。然后把静态crypto maps绑定到接口上。
配置一个名为dyn1的动态crypto maps,配置30号入口(号码随便填写),匹配ACL名为goIntoTunnel(该ACL已在之前设置好),数据连接参数为trans1(该参数已在之前设置)。
crypto dynamic-map dyn1 30 match address goIntoTunnel
crypto dynamic-map dyn1 30 set ikev1 transform-set trans1
将该动态crypto maps绑定到静态crypto maps上
crypto map mymap 50 ipsec-isakmp dynamic dyn1
将静态crypto map 绑定到outside并设置为enable, 上面已介绍过。
crypto map mymap interface outside
crypto ikev1 enable outside
设置允许IPSEC的数据包进入防火墙
sysopt connection permit-vpn
设置192.168.1.0的数据包通过outside接口进行发送
route outside 192.168.1.0 255.255.255.0 192.168.2.1
ASA2配置完毕。
两个防火墙设置完毕后,只能从发起端的PC发送数据包请求通过隧道,才会触发ipsec连接(因为接收端的配置里没有发起端的IP地址信息)。可以从PC1(192.168.1.2)ping PC3(192.168.3.2)触发设备建立IPsec连接。可以使用show crypto isakmp sa查看控制连接是否建立,使用show crypto ipsec sa查看数据连接是否建立。如下图所示:

两个防火墙的所有配置如下:
ASA1配置:
ASA1(config)# show run
: Saved
:
: Serial Number: 9AG0P7LU00M
: Hardware: ASAv, 2048 MB RAM, CPU Pentium II 3591 MHz
:
ASA Version 9.9(2)
!
hostname ASA1
enable password $sha512$5000$YZTh8YIpAhQedXT5xcZWPA==$JdPEXF2OhJ0ZMD4BelIvdQ== pbkdf2
names
!
interface GigabitEthernet0/0
nameif inside
security-level 100
ip address 192.168.1.1 255.255.255.0
!
interface GigabitEthernet0/1
nameif outside
security-level 0
ip address 192.168.2.1 255.255.255.0
!
interface GigabitEthernet0/2
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/4
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/5
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/6
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
shutdown
no nameif
no security-level
no ip address
!
ftp mode passive
object network ASA1-inside
subnet 192.168.1.0 255.255.255.0
object network ASA2-inside
subnet 192.168.3.0 255.255.255.0
access-list goIntoTunnel extended permit ip 192.168.1.0 255.255.255.0 192.168.3.0 255.255.255.0
pager lines 23
mtu outside 1500
mtu inside 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
arp rate-limit 8192
nat (inside,outside) source static ASA1-inside ASA1-inside destination static ASA2-inside ASA2-inside
route outside 192.168.3.0 255.255.255.0 192.168.2.2 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
timeout conn-holddown 0:00:15
timeout igp stale-route 0:01:10
user-identity default-domain LOCAL
aaa authentication login-history
no snmp-server location
no snmp-server contact
crypto ipsec ikev1 transform-set trans1 esp-3des esp-sha-hmac
crypto ipsec security-association pmtu-aging infinite
crypto map mymap 10 match address goIntoTunnel
crypto map mymap 10 set peer 192.168.2.2
crypto map mymap 10 set ikev1 phase1-mode aggressive
crypto map mymap 10 set ikev1 transform-set trans1
crypto map mymap interface outside
crypto ca trustpoint _SmartCallHome_ServerCA
no validation-usage
crl configure
crypto ca trustpool policy
auto-import
crypto isakmp identity hostname
crypto isakmp nat-traversal 30
crypto ikev1 enable outside
crypto ikev1 policy 1
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 28800
telnet timeout 5
ssh stricthostkeycheck
ssh timeout 5
ssh version 2
ssh key-exchange group dh-group1-sha1
console timeout 0
console serial
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
dynamic-access-policy-record DfltAccessPolicy
tunnel-group ASA2 type ipsec-l2l
tunnel-group ASA2 ipsec-attributes
ikev1 pre-shared-key *****
isakmp keepalive threshold 20 retry 3
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns migrated_dns_map_1
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map global_policy
class inspection_default
inspect dns migrated_dns_map_1
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
policy-map type inspect dns migrated_dns_map_2
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:c030dd47ce46973d8811b1556136f85a
: end文章来源:https://www.toymoban.com/news/detail-836083.html
ASA1(config)#
ASA2配置:
ASA2(config)# show run
: Saved
:
: Serial Number: 9AA4EG8LNAD
: Hardware: ASAv, 2048 MB RAM, CPU Pentium II 3591 MHz
:
ASA Version 9.9(2)
!
hostname ASA2
enable password $sha512$5000$BgWr3rLdxm3i+QSJKnW9QQ==$J7iDqV+4n52S34mxjxrF2A== pbkdf2
names
!
interface GigabitEthernet0/0
nameif inside
security-level 100
ip address 192.168.3.1 255.255.255.0
!
interface GigabitEthernet0/1
nameif outside
security-level 0
ip address 192.168.2.2 255.255.255.0
!
interface GigabitEthernet0/2
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/4
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/5
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/6
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
shutdown
no nameif
no security-level
no ip address
!
ftp mode passive
object network ASA1-inside
subnet 192.168.1.0 255.255.255.0
object network ASA2-inside
subnet 192.168.3.0 255.255.255.0
access-list goIntoTunnel extended permit ip 192.168.3.0 255.255.255.0 192.168.1.0 255.255.255.0
pager lines 23
mtu outside 1500
mtu inside 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
arp rate-limit 8192
nat (inside,outside) source static ASA2-inside ASA2-inside destination static ASA1-inside ASA1-inside
route outside 192.168.1.0 255.255.255.0 192.168.2.1 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
timeout conn-holddown 0:00:15
timeout igp stale-route 0:01:10
user-identity default-domain LOCAL
aaa authentication login-history
no snmp-server location
no snmp-server contact
crypto ipsec ikev1 transform-set trans1 esp-3des esp-sha-hmac
crypto ipsec security-association pmtu-aging infinite
crypto dynamic-map dyn1 30 match address goIntoTunnel
crypto dynamic-map dyn1 30 set ikev1 transform-set trans1
crypto map mymap 50 ipsec-isakmp dynamic dyn1
crypto map mymap interface outside
crypto ca trustpoint _SmartCallHome_ServerCA
no validation-usage
crl configure
crypto ca trustpool policy
auto-import
crypto isakmp identity hostname
crypto isakmp nat-traversal 30
crypto ikev1 policy 1
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 28800
telnet timeout 5
ssh stricthostkeycheck
ssh timeout 5
ssh version 2
ssh key-exchange group dh-group1-sha1
console timeout 0
console serial
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
dynamic-access-policy-record DfltAccessPolicy
tunnel-group ASA1 type ipsec-l2l
tunnel-group ASA1 ipsec-attributes
ikev1 pre-shared-key *****
isakmp keepalive threshold 20 retry 3
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns migrated_dns_map_1
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map global_policy
class inspection_default
inspect dns migrated_dns_map_1
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
policy-map type inspect dns migrated_dns_map_2
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:b64ac3c3d10f45ee6d61cb3617a4dd7b
: end
ASA2(config)#文章来源地址https://www.toymoban.com/news/detail-836083.html
到了这里,关于思科防火墙IPsec配置-野蛮模式方式(基于9.9版本)的文章就介绍完了。如果您还想了解更多内容,请在右上角搜索TOY模板网以前的文章或继续浏览下面的相关文章,希望大家以后多多支持TOY模板网!